I’ve been a little bit busy the last few months and here’s why – my first Pluralsight course, the OWASP Top 10 Web Application Security Risks for ASP.NET. Actually, if I’m honest, it’s been a lot longer than that in the making as my writing about the OWASP Top 10 goes all the way back to right on three years ago now. It begin with the blog series followed by the free eBook then last year the instructor lead training for QA and now finally, a complete online video course via Pluralsight.
For the uninitiated, Pluralsight is what they call “hardcore developer training” and it’s predominantly produced by fellow MVPs, community leaders and other subject matter experts who many of you would be very familiar with (there’s a great little article on TechCrunch with a very glowing overview of Pluralsight here). The quality of Pluralsight’s authors really are top notch and it is an honour to be able to contribute to my own little corner of expertise. The content is subscription based and starts at only $29 per month (and there’s a free 10 day, 200 minute trial if you’re not sure). You can watch it online via the browser or native clients for a variety of devices and depending on your subscription level, even save the courses offline.
Pluralsight as a training service is an absolutely fantastic resource and one I have used on many, many different occasions now. The breadth of content is huge and includes everything from the latest enhancements to ASP.NET 4.5, nitty gritty detail about LINQ, lots of fancy tricks in Entity Framework and a heap more in the ASP.NET space. Then of course you’ve got everything you could want to know about client technologies such as jQuery, CSS, HTML and on and on. Take a spin through the top courses and you start to get a sense of the breadth of content.
One thing I’ve learnt working with a bunch of different people over the years is that everyone has their own style of learning. We all like absorbing information in different ways and what I like about the structure of Pluralsight is that you have the choice to either sit through an entire course and go through in a very structured fashion, pick just one module on a discrete topic and learn everything about it or drill down even further and just pick one clip from within the module.
I’ve used each of these approaches in the past, most recently when I really wanted to get up to speed on Entity Framework 5 enum support. There’s plenty of info out there on this but I knew that Julie Lerman is the person when it comes to EF so I spent 6 minutes watching that topic in her Getting Started with Entity Framework 5 course and had exactly what I needed to, well, get started!
Let me tell you a little more about what I’ve created.
What’s in the OWASP Top 10 for .NET developers course?
Getting back to my own course, there are (unsurprisingly) 10 modules that align to the OWASP Top 10. This now very familiar list includes:
- Injection
- Cross-Site Scripting (XSS)
- Broken Authentication and Session Management
- Insecure Direct Object References
- Cross-Site Request Forgery (CSRF)
- Security Misconfiguration
- Insecure Cryptographic Storage
- Failure to Restrict URL Access
- Insufficient Transport Layer Protection
- Unvalidated Redirects and Forwards
What I think is important though is how I’ve structured these modules. You see, my view is that for developers to really grok security concepts they need to see it in action. Of course they need to understand the principles behind it as well, but there’s nothing quite like seeing password hashes cracked or wireless traffic sniffed, that stuff really hits home. I also believe that it’s absolutely essential that risks are related back to practical instances where they’ve been exploited so every module has an industry precedent it refers to. It’s very easy to treat a risk as hypothetical or academic until someone actually goes and does nasty things with it then suddenly everyone starts paying attention (Firesheep was a great example of this in terms of the risk of not having SSL everywhere).
What all this means is that each module is broken down like this:
- An introduction to the topics that will be covered in the course
- The OWASP overview of the risk including severity, threat agents and attack vectors
- Anatomy of an attack – this is the interesting bit as it involves exploiting the app
- The risk in practice where there’s been a precedent of it being exploited in the industry
- Mitigation demos – usually four or five ways of mitigating the risk
- Further information on the risk via slides or more demos
It’s a very practical course with most of it living in Visual Studio and the browser then where it adds value or just needs further explanation there’s info and graphics on slides. Certainly the preference is always to demonstrate though as again, practical relevance is what really helps security principles hit home.
All in all, there’s 8 hours and 6 minutes worth of content with some modules being relatively short (broken auth and session managements is under half an hour) and others being more comprehensive (transport layer security is nearly one and a quarter hours). I’ve tried to only include content of tangible benefit and break them down into very discrete units. Whilst 8 hours is quite long for a Pluralsight course, there are 121 clips in total so you’re looking at about 4 mins each. The longest is just over 11 mins and demonstrates an attacker sniffing wireless traffic whilst the victim browses a website then has their session hijacked due to insufficient transport layer protection. IMHO this is the best piece of content in the whole thing!
How should you take this course?
Like I said earlier, everyone likes learning differently and I totally get that some people like bite-sized information about discrete topics and others want to absorb things in a more formal, structured fashion. How you take this course will also come down to your familiarity with the topic; you may have a good understanding of the intricacies of SQL injection but CSRF remains a bit strange. Perhaps XSS is familiar but why unvalidated redirects are a risk seems odd.
What I will say though is that many of these risks have interdependencies and the course material does touch on this at multiple stages throughout the modules. I talk a lot about whitelists which are first introduced in the SQL injection module, the membership provider concepts in the third module on broken authentication are then reused at multiple points such as when I talk about cryptographic storage. The course builds on itself, module by module.
Ideally, absorb the whole thing piece by piece and in sequence. The assumptions I make about the material that has already been covered and the knowledge gained will make a lot more sense. There are also various segue ways into tangential security issues throughout the modules so they do cover more than just what the name might imply.
Why should you take this course?
We have a problem. As developers, we’ve got a lot to answer for and you see the results of security shortcuts on the news on a daily basis. As I’ve written before, the problem with website security is us. We are the ones designing the systems which expose excessive data, leak error messages and fail to properly secure credentials. Sometimes these are decisions made beyond our control with full consciousness of the risks but more often than not, it’s “us” thinking that encoding is encryption, that our admin systems are safe because nobody knows they’re there and that salting and hashing passwords is enough. It’s not, they’re not and it isn’t.
In so many of these cases it would have taken just one person on the development team to say “Hey, let’s think twice about this” and disaster would have been averted. But of course you don’t know what you don’t know and that’s why the education component is so critical.
My overwhelming strongly held belief – and this isn’t just about security – is that we must invest in our developers. The difference in cost between the good ones and the bad ones is a paltry sum (if indeed the good ones earn any more at all) but the difference in effectiveness is measured in an order of magnitude. When you do look at it in the context of security, investing in education will always seem like an excellent idea in hindsight. Whilst First State Super was looking down the barrel of losing a $23m contract because the developers didn’t understand the simple risk of insecure direct object references, security education must have seemed like a fine idea and there are many, many similar examples.
If security is important to you as either a developer or someone responsible for a development team, find a day. Just one day and you’ll get all the way through the course. Do it over a week and knock a couple of hours of each day before coffee break and you’re done. For most developers, they’ll end that week having learnt a whole lot of totally new stuff and who knows, it may quite possibly one day save their employer from ending up on the front page of the news.
Inside the sausage factory
Moving away from the course content itself, I thought some people might be interested in what goes into creating a Pluralsight course as there’s a lot more to it than what you might assume from face value alone. Firstly, for a new author such as myself there’s an audition process and a pitch; you’ve got to have both good content and be able to deliver it to Pluralsight’s standard. As an author, there’s a bit of work involved but as a customer, you really appreciate this as it means you get a consistent high-quality experience across courses.
Once all that’s ticked off the real hard work begins. For each module I produced I’d work out a series of clips and create a run-sheet of how I’d execute each one. This involved preparing slides, a sample app and then usually doing a dry-run of each clip before recording it. When everything was ready I’d drop a screen back to 1024x768 (the default video resolution) and try to record the whole thing in one go with Camtasia. Kind of.
I say “kind of” because although it’s one go, every time I so much as stuttered or ummed or rambled ever so slightly, I’d record it again. This is what killed me with this course because I just didn’t want to produce anything I didn’t feel was absolutely perfect. I’ve seen plenty of video material in the past that just wasn’t slick – those little glitches really irk me and I wasn’t going to be letting any of them into my course. What it meant though is that there’s rarely more than 10 seconds of video that was recorded in one continuous flow. That’s not because I continually made errors (there’s a degree of that), but rather because I wanted to get a clear message across then think very, very carefully about what made sense next.
Sometimes I found myself having to stop and say “Ok, when I produce this, go back to that earlier section then overlay the audio I’m about to record into the middle”. Other times I’d have to re-record audio when I listened to it later on during editing because an important part of the story was missing, I’d just skipped it in the excitement of the recording. What it means is that my Camtasia timelines all look like this:
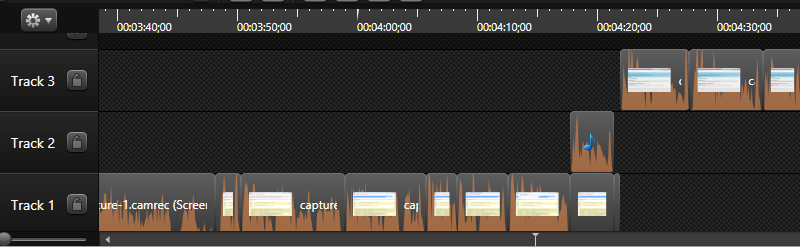
What you’re seeing here is lots of chopping and editing just to get everything lining up perfectly. It ain’t pretty to look at, but it makes a lot of difference to listen to.
All of this comes at a cost – a time cost. Just to give you a rough idea, here’s how I reckon it breaks down for every minute of produced video you watch:
- 3 minutes of preparation (run sheet, sample app, slides, general research)
- 2 minutes of captured video
- 7 minutes of editing
- 2 minute of producing, packaging slides, app and assessment
In other words, every time you watch a minute of video it has taken about 12 minutes to get it to where it is. Across 8 hours and 6 mins of content that’s about 113 hours of work. That doesn’t sound too bad, but it’s amazingly monotonous, at least the editing is. It basically means I’ve spent my evenings and weekends for the last few months looking at this:
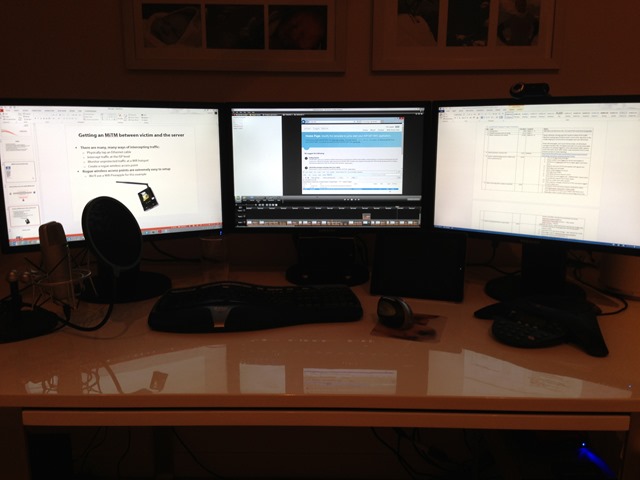
I started all this at the end of Jan and in amongst all this I had numerous dramas to deal with including needing to completely rebuild my machine after a catastrophic crash, trying to schedule recording around noisy kids, re-recording an entire clip due to noisy kids in the background and being away at the MVP summit for a week. It also finally pushed me into getting properly acquainted with my Pineapple (it makes an appearance in the section on transport layer protection) which was a very lengthy (and ultimately very fulfilling) process.
This was an epic piece of work but I’m enormously happy with the result, it’s undoubtedly the most comprehensive, polished tutorial I’ve produced to date.
What’s next?
I have some ideas… no really, over the last six weeks as the end has begun to come into sight I’ve started jotting down notes for a new security course that’s quite a bit different to this one. In fact I think I have a great angle, all I need is for this course to prove popular enough for Pluralsight to want to invite me back, so it’s up to you now!
