A few weeks back there was a great document released by Verizon (yep, the big American telco) titled Verizon 2012 Data Breach Investigations Report. This weekend at the OWASP Appsec Asia Pacifica Conference, I sat in on a talk from Mark Goudie from Verizon who helped put the whole report in perspective. Now this is a really interesting report because rather than talking about vulnerabilities (i.e. potential risks), they’re actually looking at exploits; this is hard facts, people!
This report is based on 855 incidents in 2011 (don’t be confused by the year in the title!) and because Verizon does this each year, there’s lots of data on how trends are changing. It’s also 80 pages of hard facts which can be rather a lot to digest. But there are some really interesting nuggets in there for those who take a bit of an interest in security. Let me cherry-pick a few of the good ones.
1. Breaches are (almost) no longer coming from inside the organisation
It wasn’t that long ago that the common belief (and there were plenty of numbers backing this up), was that a significant portion of breaches stemmed from inside the organisation. Disgruntled employees, opportunistic mutineers, those off to greener pastures grabbing a handful of data on their way out – whatever – but it’s now a very different story:
| Who is behind data breaches? | |
| 98% stemmed from external agents (+6%) | No big surprise here; outsiders are still dominating the scene of corporate data theft. Organized criminals were up to their typical misdeeds and were behind the majority of breaches in 2011. Activist groups created their fair share of misery and mayhem last year as well—and they stole more data than any other group. Their entrance onto the stage also served to change the landscape somewhat with regard to the motivations behind breaches. While good old-fashioned greed and avarice were still the prime movers, ideological dissent and schadenfreude took a more prominent role across the caseload. As one might expect with such a rise in external attackers, the proportion of insider incidents declined yet again this year to a comparatively scant 4%. |
| 4% implicated internal employees (-13%) | |
| <1% committed by business partners (<>) | |
| 58% of all data theft tied to activist groups |
Going back to that earlier comment about attacks previously often coming from inside, take a look at how the data has changed over time:
Threat agents over time by percent of breaches:
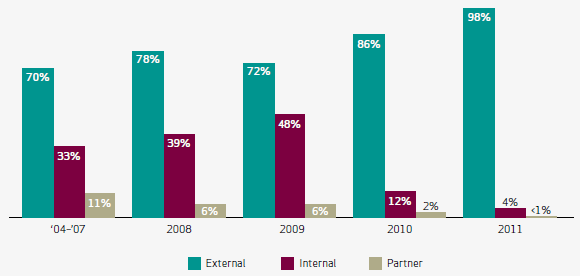
Or to put it another way, breaches originating internally are now only 12% of what they were a few years ago and breaches from partners are near non-existent. The bad guys are now well and truly outside the organisation – but they’re still getting in.
Oh – and in case you’re wondering why 98% plus 4% plus under 1% adds up to more than 100%, some breaches span both external and internal players. For example, someone external socially engineers someone internal into divulging their credentials. Makes sense now!
2. Hacktivists are becoming seriously bad news
This shouldn’t come as a surprise, but the number above is still alarming; 58% of data theft was tied to individuals purporting to carry out their illegal activities on the basis of some form of activist belief. Frankly, when you look at the demographic of those being caught in the act (frequently teenagers or early 20’s), I suspect that whilst these individuals are readily attaching themselves to hacktivist groups such as Anonymous and LulzSec, it’s more about gaining a bit of notoriety and having some lulz than it is about fighting for a cause.
From the report:
The most significant change we saw in 2011 was the rise of “hacktivism” against larger organizations worldwide.
Regardless of the motivations of hacktivists, the fact remains that there is a groundswell of individuals out there queuing up to take a shot at just about any website they can get their hands on. They don’t need the financial incentive of true cybercriminals or the political and military goals of nation states, they just need an easy target. Frankly, for website owners, this indiscriminate targeting should be rather worrisome.
3. The majority of breaches are related to simple credential theft
Here’s an interesting one; how do you think most hacks are being carried out these days? Some funky SQLi? Sneaky 0-day exploits? Not quite:
Threat Action Types by number of breaches
| Variety | Category | Breaches |
| Use of stolen login credentials | Hacking | 30% |
| Backdoor (allows remote access/control) | Malware | 18% |
| Exploitation of backdoor or command and control channel | Hacking | 17% |
| Tampering | Physical | 17% |
| Keylogger/Form-grabber/Spyware (capture data from user activity) | Malware | 13% |
| Pretexting (classic social engineering) | Social | 12% |
| Brute force and dictionary attacks | Hacking | 8% |
| SQL injection | Hacking | 8% |
| Phishing (or any type of *ishing) | Social | 8% |
| Command and control (listens for and executes commands) | Malware | 8% |
The use of stolen credentials is, relatively speaking, off the chart. Nearly a third of breaches involved the theft of credentials (among other vectors – another one of these does-not-add-up-to-100% scenarios), which is quite astounding. I say this because obviously once credentials are obtained, the “hack” itself may be very unsophisticated indeed.
Of course the bigger question this raises is “How are these credentials being stolen?” The report alludes to keyloggers and spyware being to blame so again, these breaches are often the result of a series of incidents opening various doors leading up to the eventual data breach.
4. You’re way more likely to be socially engineered by talking to someone than via email
Social engineering is what happens via email, right? I mean there is a common belief that modern social engineering is something which predominantly has its roots online – or perhaps that was just my belief. The numbers, however, paint a very different story:
Social vectors by percent of breaches within Social
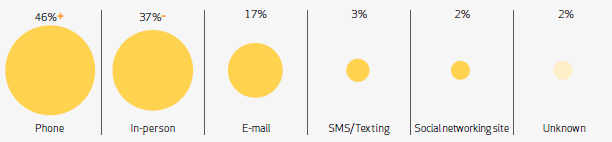
What strikes me as surprising with these numbers is that the phone and in-person vectors both involve actually talking to and verbally engaging with the victim. The veil of anonymity provided via email and social networking sites is not there; the attacker has to respond on the spot with credibility and actually convince their victim to divulge information or perform activities they wouldn’t (or at least shouldn’t) normally do.
On the other hand, nobody expects the Spanish inquisition; putting a voice – or even a face – to an attacker gives them enormous leg-up over a random phishing email when it comes to actually establishing some credibility. I recently read Kevin Mitnick’s Ghost in the Wires and when you consider how easily he was able to gain trust and leverage his victims’ good nature against their better judgement, the figures above perhaps don’t seem so surprising.
5. Breaches take only minutes yet are discovered after months – and then they take a long time to fix
How much effort does it actually take to breach a vulnerable target? Apparently you can measure it in minutes:
Timespan of events by percent of breaches
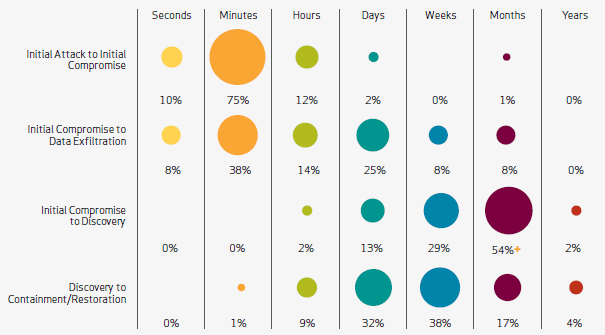
The significant bulk of results falling into the “Minutes” category suggest that most breaches recorded by Verizon are very simple affairs. We’re talking 85% of them taking minutes or even less (I assume “Seconds” would imply some form of automation).
But the other stunning fact here is how long it takes to actually discover the compromise after the fact; “Months” is very bloody long time! So someone has broken in, stolen your data and by the time you realise it, they’re looooong gone.
The last row is also concerning because it says that more than half the time it takes at least some weeks to fully plug the hole and get back to business as usual. Think about the business impact of this – we’re taking a major adverse outcome in many of these cases.
You know what the most interesting stat is? It’s the one that’s not in the chart above but would be simply titled “Attacks that were never discovered”. Now of course by its very nature we’re never going to see this charted, but the very fact that it more often than not takes months to discover a breach, there are undoubtedly a significant number that go undiscovered. Forever. In fact the report does make a mention of this:
We hypothesize that many insider crimes go unreported because the organization is unaware of them, or because they decide for political reasons to handle it internally.
Makes you wonder who has been in your systems without you ever even realising, doesn’t it?
Other interesting titbits
On PCI compliance:
We still hear the common mantra “How could I have been breached?—I’m compliant!” We cannot stress enough that while compliance definitely helps drive security, compliance does not equal security.
Does anyone really think that being PCI compliant alone means you’re “unhackable”?! I suspect the big compliance sticker appeals to those who perhaps don’t have a great appreciation of the finer points of software security and it is those same individuals who are quoted above. Just sayin’.
On the variety of hacking attacks:
Like every year, a handful of techniques dominate the charts. Generally, the hit parade can be subdivided into the authentication attacks, and technical attacks that bypass or break authentication altogether.
Now this covers everything from exploiting default (yes – default!) or guessable credentials, the use of stolen credentials and brute forcing auth systems. It’s interesting to juxtapose this with the OWASP Top 10; no injection, no XSS (the “Top 2”), rather its third on the list – “Broken authentication and session management”.
On attacks against larger organisations:
So, what about larger organizations? Surely they’re a lot more difficult to infiltrate, right? Sadly, our data seems to suggest otherwise; it does not appear that cybercriminals have to work much harder to compromise larger organizations than they do for smaller ones.
Frankly, I think that any assumptions about larger organisations being harder attack targets is folly. We know from previous studies that the vast majority of breaches occur at the software layer and my view – which some may dispute – is that developers are developers are developers. Let me explain: these guys (of which I consider myself one), are the ones introducing the vulns and while some organisations invest more in their security education than others, I see no evidence that larger organisations take the security competency of their developers any more seriously than smaller organisations. The figures would seem to support this.
On social engineering:
The “carbon layer” of information assets (the user) is notoriously susceptible to social tactics such as deception, manipulation, and intimidation, and savvy threat agents know how to use this to their advantage.
I just like this one because I’ve never heard of the user being referred to as the “carbon layer” before. Nice :)