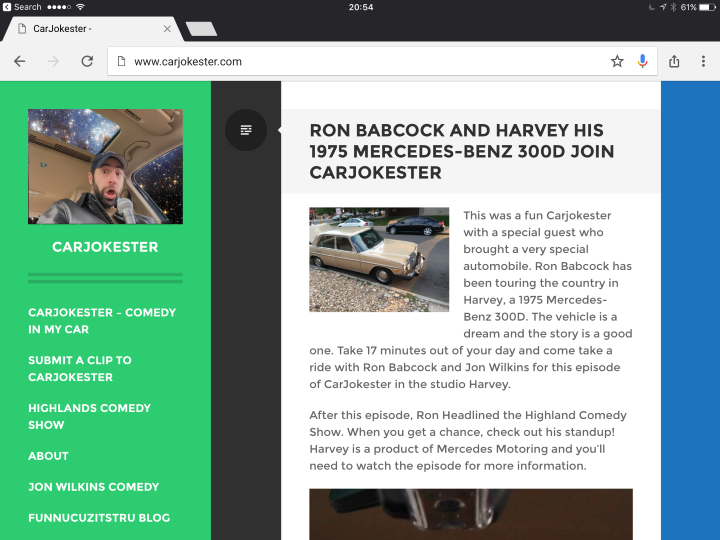
I was shopping around for a new exhaust system for the car the other day and I found exactly what I wanted via a seller on Facebook. I really wanted to get some more specs on it though so I did what any normal person would do and Googled for it, finding a result titled "Boost Logic Nissan R35 GT-R 4" Titanium Exhaust" and linking through to a page on the official Boost Logic website. However...
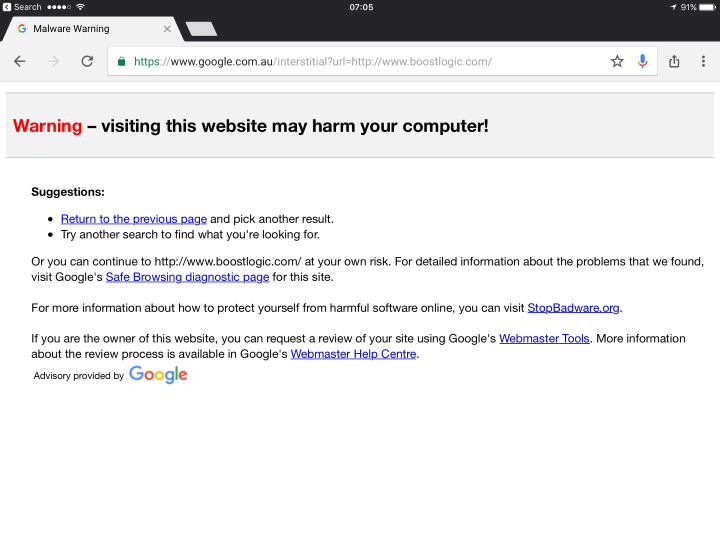
Now this, clearly, isn't a good look. This is the official site and not a spoof or phishing site, yet Google had just put up a massive barrier to entry. It got me thinking about the old adage we hear so many times in security, the one that goes like this:
But we don't have anything of value on our site anyway
This defence is frequently preceded by an observation of a security deficiency somewhere and a suggestion that perhaps they're taking unnecessary risks. The opinion that many hold is that without the presence of credit cards or passwords or some other piece of useful data, the site simply doesn't pose any value to malicious parties.
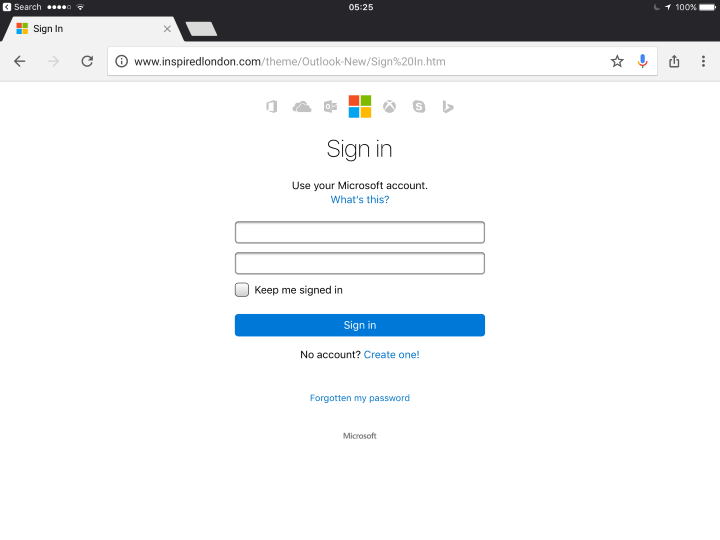
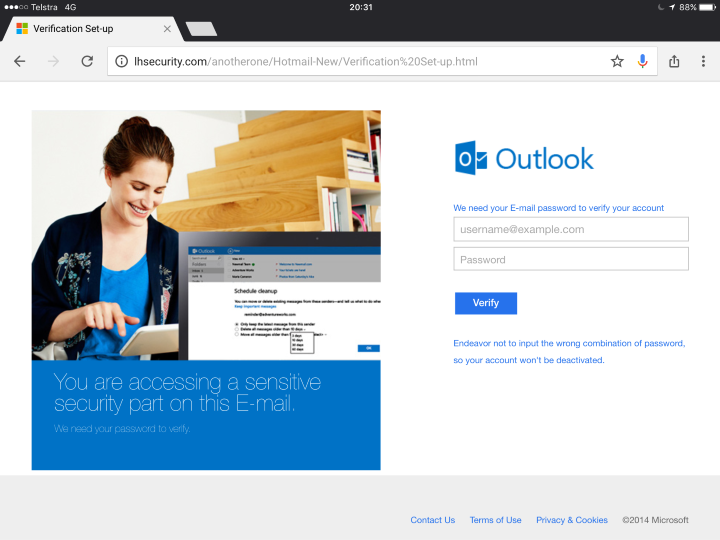
This all got me thinking about the value of reputation and how it's exploited by malicious parties. I started looking around at some of the spam I was receiving (often bypassing spam filters), and saw the same patterns over and over again. For example, it was suggested that I may need to login to my Outlook account to fix some problems:
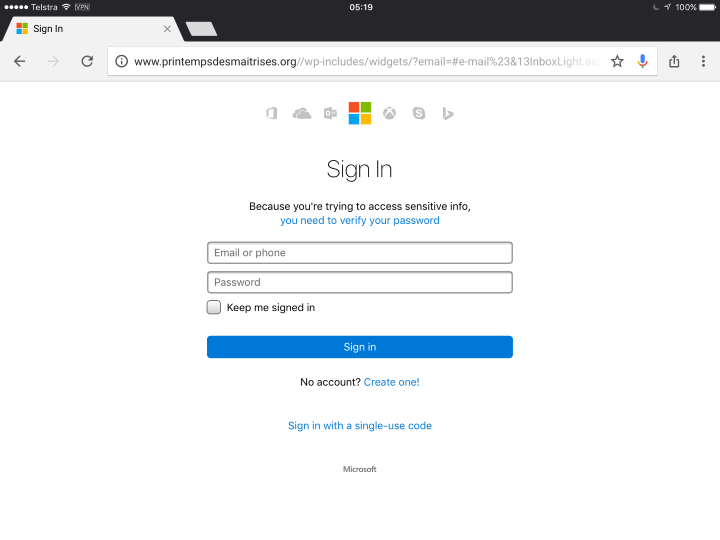
That's actually a pretty slick looking phishing page but the domain gives it away. Here's the actual site which as best I can tell from Google Translate, is a French Wordpress site about a kids choir event:

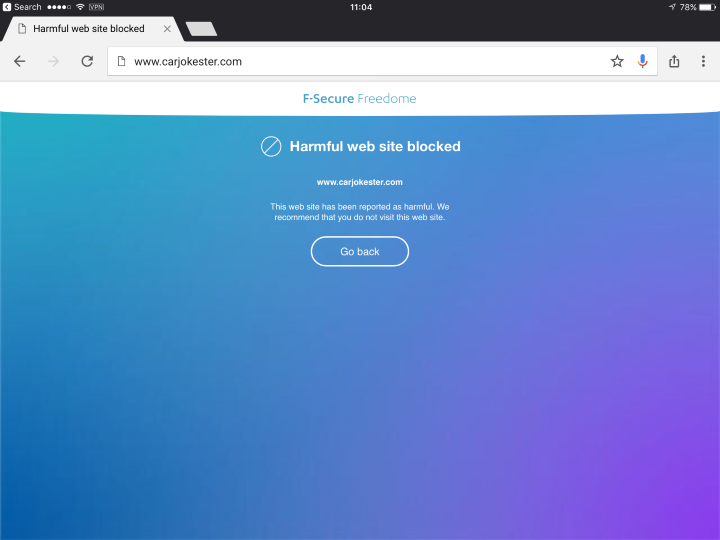
Look carefully though and you might notice the two images above show my VPN enabled. That's because when I tried to load it direct via my broadband connection at home, it did this:
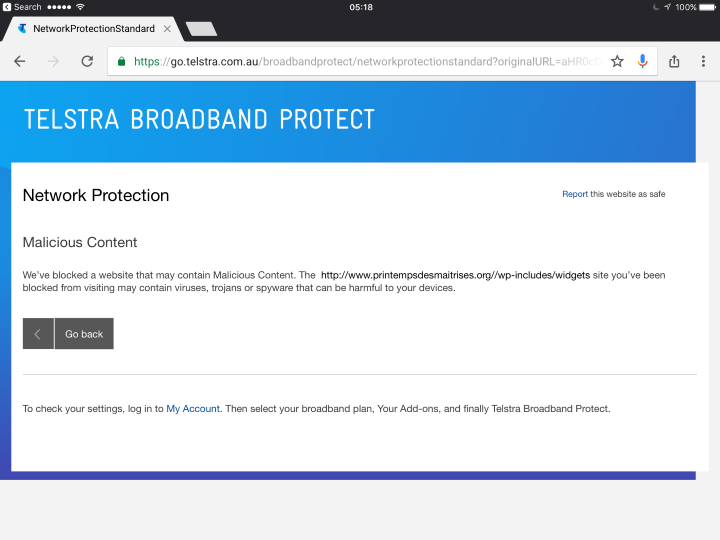
This is reminiscent of the Boost Logic site earlier on where there's an upstream control blocking what has been identified as a malicious site. Oddly though, I can use the exact same telco but on my 4G connection and the page loads without being blocked.
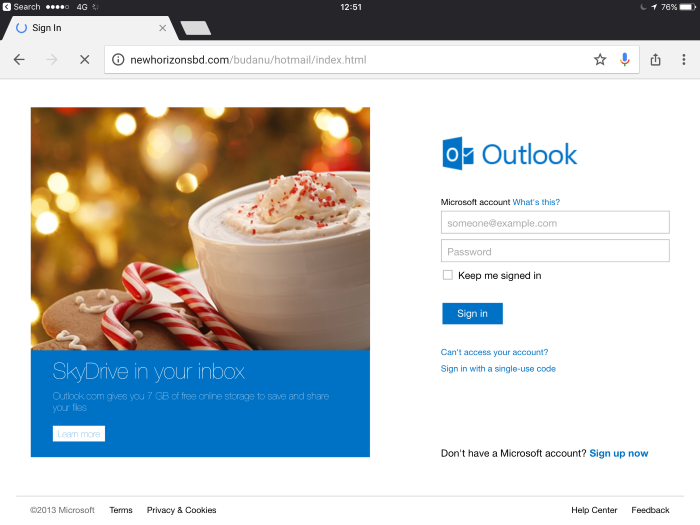
And that's the other thing that's noteworthy with the way content is blocked - it's very inconsistent. For example, here's another pretty well put together Outlook phishing page:
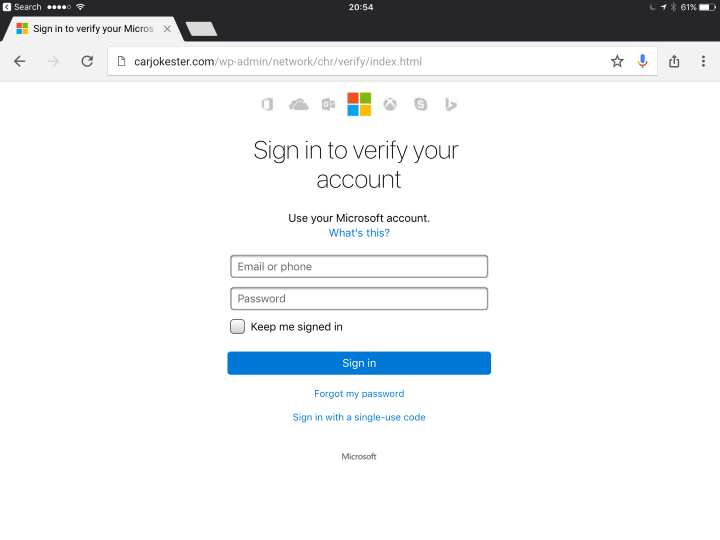
Same deal as the earlier one in that it's an otherwise very innocent website behind it, except that this time both of them happily load over my home broadband connection:
But now here's a twist - I turn on my VPN (I use Freedome) and that's it - the site is now cactus:
You might have noticed I'm using the iPad for each of these tests as frankly, I've got a much greater degree of confidence that a heavily sandboxed iOS running without plugins is more resilient to nasty things. But let's give that last one a go in Chrome on the desktop anyway, just for a quick look:
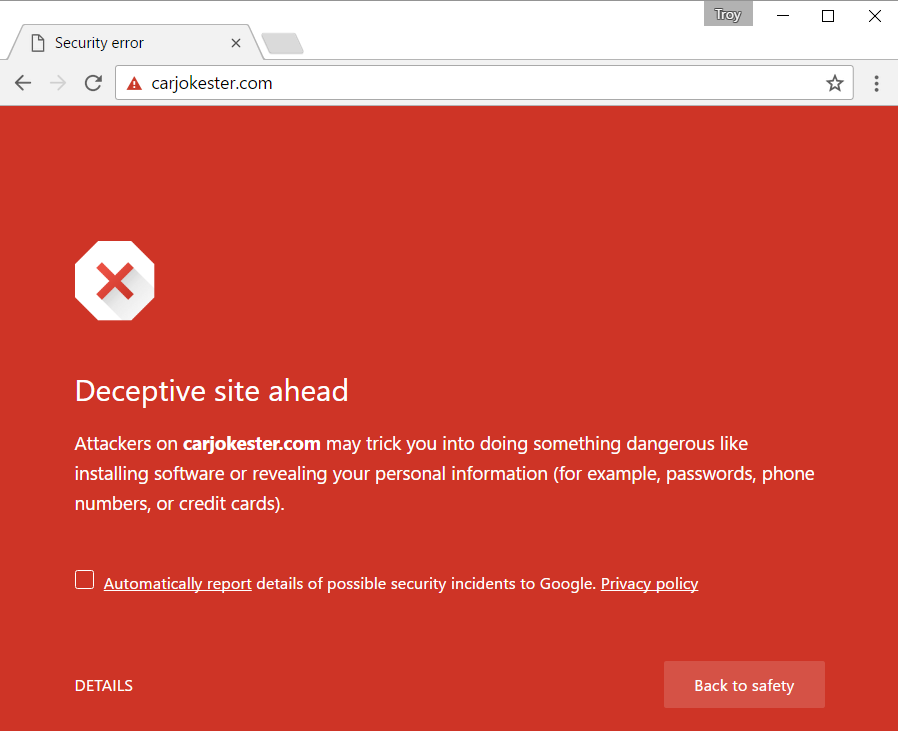
And that's that site now pretty much dead in the world's most popular browser.
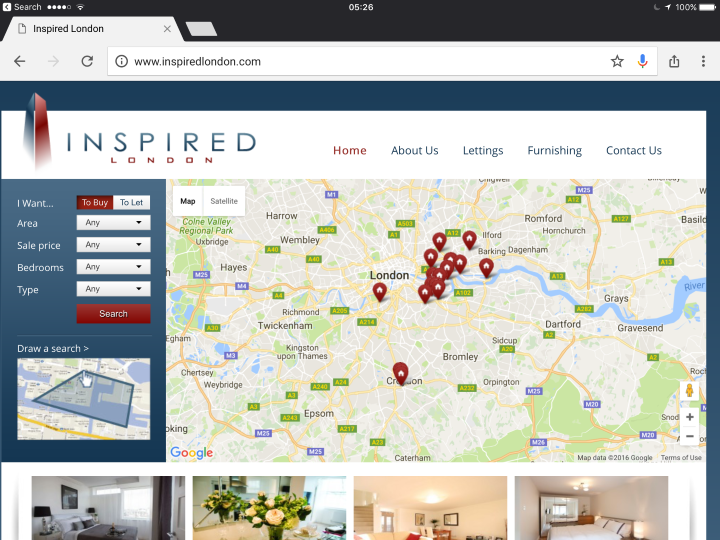
The same story plays out again and again and again. Another Outlook login page:
Which is just a London real estate site:
Outlook again (you seeing a theme here yet?):
Except it's not, it's actually a provider of security services (never a good look to have that sort of thing pwned!):

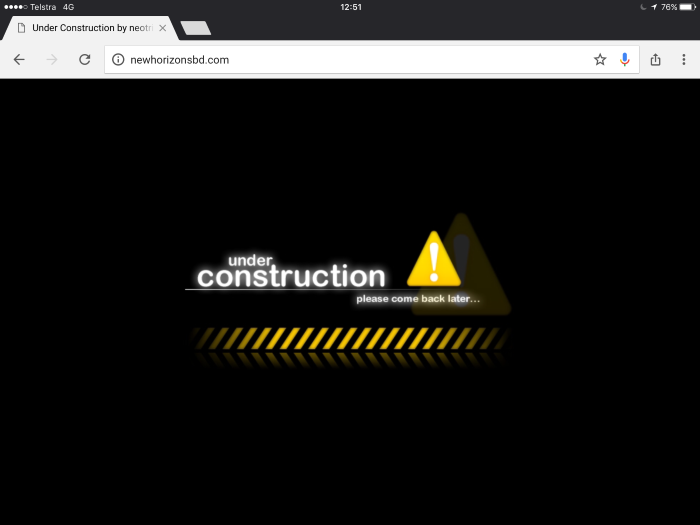
Even more Outlook:
And this page doesn't even have anything on it yet:
But this is really the point of the whole post and indeed the title of the page: the value your site has to attackers is not just the data, it's the reputation. It doesn't even need to be a good reputation in terms of it being a well-established site with lots of inbound links, it simply needs to be a site that doesn't have a bad one. That's the value to attackers - a launchpad that's not blocked by any of the mechanisms I showed above - and there's a very small opportunity to exploit that reputation before large swathes of people are blocked from the site altogether.
And just as one final adjunct to the story, this one happened just yesterday:
@troyhunt Either I have an incorrect setting or the guys at Norton are screwed up... I am certain it's not you. pic.twitter.com/UqjxO8wTOq
— Charles R. Smith (@softwarnet) December 21, 2016
To say I was surprised is an understatement! In this case, my blog was just fine but because I had one file on a totally different sub-domain that was classified as a "hacking tool", here we are. Fortunately everything came good as soon as I hid deleted it, but it just goes to show how fickle reputation can be.
So there it is: many different examples of why whether you know it or not, your site has something valuable to attackers, it just may not be what you originally thought it was.