To date, I’ve avoided commenting on the other Ashley Madison search services and have invested my efforts purely in keeping Have I been pwned? (HIBP) ticking along. I’ve seen them come and indeed I’ve seen some of them go too. I’ve seen many that enable you to get confirmation about the presence of an email in Ashley Madison, others that return everything about the user. Publicly. To anyone.
But something I saw today struck a very different chord with me, something that I found to be truly outlandish. Let’s try an exercise; have a careful look at this page and read through all the information on it:
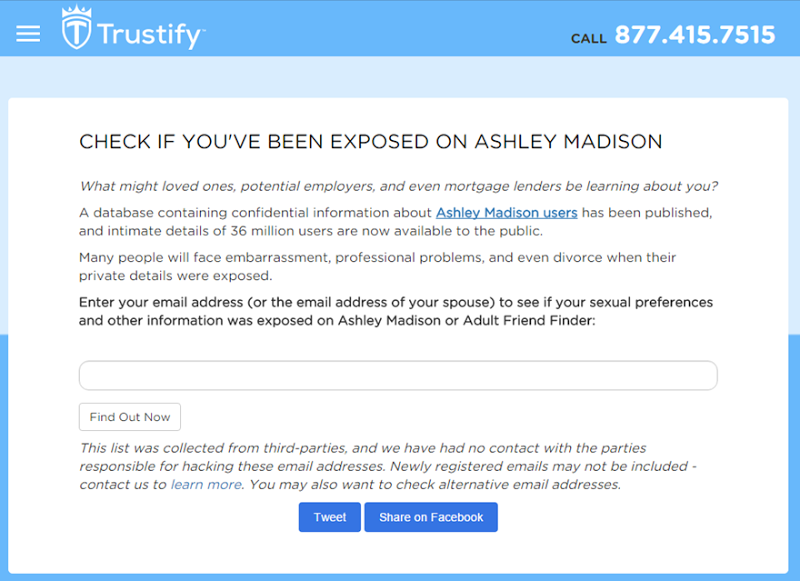
Can you see the section that explains the site will store the email address you search for? No, I didn’t think so.
Can you find the bit about it emailing the address you search for if it has a hit in the Ashley Madison database? Me either.
Or how about the bit that explains whoever’s email address this is will receive a solicitation for Trustify’s services if they’re in the Ashley Madison database? Yeah, that’s missing too, but here it is:
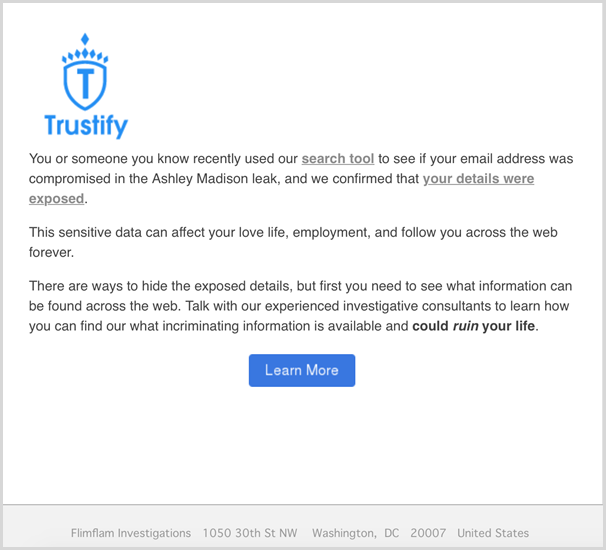
I had this forwarded to me earlier today and frankly, I couldn’t believe it. I mean I knew Trustify was making email addresses publicly searchable and somehow not falling foul of DMCA takedowns whilst others doing the same thing were (possibly because Trustify has more lawyers than employees), but I had no idea they’d actually harvest addresses and then send unsolicited emails, so I Googled a bit and found a very unsympathetic Reddit thread on it. There’s a series of responses from thejournalizer (reportedly the content marketing director at Trustify) which provide such enlightening insights as:
The email OP received was actually established to help you and warn you that someone is seeking out details about you.
Ah, it’s there to help you! So after you search on the site and it says “You’ve been compromised” and provides a handy form to sign up to their commercial services, an email is also sent to you because, well, it might not be you. The design of the system specifically recognises that people will search for other people and that it presents an opportunity for those other people to then receive marketing about Trustify services.
Someone even suggested that perhaps it would be more responsible to take the same approach as I have with HIBP and and only show results to verified users, but apparently this isn’t possible:
Legal gave me the response of we are unable to alter the results.
Ah, it’s Legal’s fault, so it’s cool to have a situation like I wrote about earlier where someone’s church is checking up on the congregation but altering the search results in the name of privacy is problematic. Someone else suggested the same thing – that they follow the HIBP approach – and thejournalizer’s response showed that they just don’t get it:
Trustify is not publishing any data publicly. It simply gives a yes or no confirmation if an email address was in the leak. No other data is available.
This is the “it’s only meta data” excuse – “hey, we’re not disclosing who the person wanted to have an affair with, all we’re doing is telling everyone that they were looking to have an affair!”
There’s more from thejournalizer on the premise of verifying identity first:
Unfortunately that makes the situation look like we are hiding people's information, and we simply can't do that
That’s the whole point! Don’t you get it – people’s lives are being ruined because their information is no longer hidden! Not handing it out left right and centre to everyone that stumbles upon it is the entire point!
Here are the real issues with their approach:
Firstly, when people use a search services like this, one of their primary fears is that their information will be used beyond the scope of what they’re providing it to you in. I know this better than anyone because I get questions about it all the time on HIBP. Harvesting of emails is precisely what people don’t want when they use a service like this.
Secondly, people will search for other people. That alone is bad enough and it’s why I kept HIBP searches confined to those who can actually demonstrate that they own the address, but to then tell the victim of the breach they’re being searched for is inconceivably bad. Keep in mind these are not people who signed up to Trustify to be notified when others are snooping around for their data, rather people who have never heard of Trustify before are getting unsolicited emails saying others are spying on them. Let’s not mince words either; The Register is already reporting that the Ashley Madison spam is starting with regards to Trustify’s practices and that’s precisely what it is – unsolicited bulk email that Trustify knows they’re sending to people who did not request it and they know this because Trustify are encouraging other people to search for victims!
Thirdly, this is exploiting the situation for profit. I use those words specifically because it’s precisely what Trustify’s page on Ashley Madison says they’re not doing (the same page that talks about their 15x increase in “caseload” since Ashley Madison). They explain that their service was already in existence before the breach and that’s fine – people were sending requests to have their exposure on the web investigated, I get that. But making the search feature wide open to the public then sending emails to unsuspecting victims of the attack encouraging them to “talk with our experienced investigative consultants” is the very definition of exploiting the situation! In fact while I mention that page, it says that “Based on customer feedback, it evolved into a tool where anyone could search for specific email addresses”. I wonder how many Ashley Madison customers said “Why yes, I think it would be marvellous if anyone in the world could anonymously discover my adulterous ways”…
And finally, keep this in mind before using a service like this: every search you do is contributing to their marketing database of potential customers built up without consent. That’s a reasonable assumption to make based on the above and it’s confirmed by a follow-up email some time later:
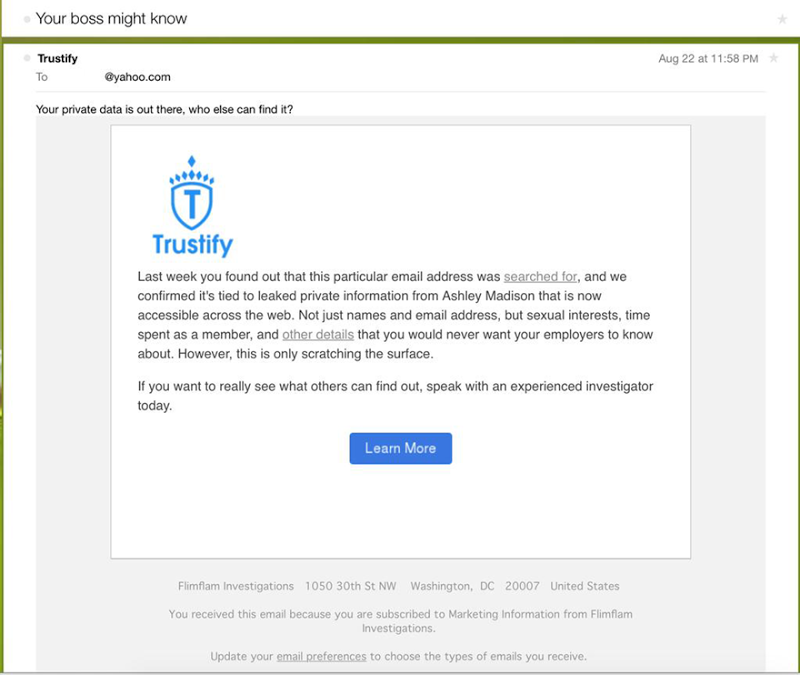
In fact its very clear what the purpose is – “you are subscribed to Marketing Information from FlimFlam Investigations” – so by searching for your address in their system, you have now inadvertently become a marketing lead. Even if you didn’t search Trustify’s Ashley Madison database yourself, you may now be recorded by Trustify as someone under suspicion of having an account just because someone else was curious. It’s unclear whether email addresses that weren’t in the Ashley Madison dump are also being harvested by Trustify; is your innocent husband’s address now there? Or your kid’s teacher? Think very carefully before entering any email address into a site like this. Do also note that I’ve said “Breach sites like Trustify” in the title of this post as I’ve no doubt that other similar sites are doing the same thing. Just for the record, no, HIBP does not harvest addresses and it’s been covered in the FAQs since the very beginning.
One other thing to point out while we’re here: Trustify emails are being sent with the subject “Your boss might know”. This is outright fear mongering designed to create a sense of desperation in the recipient of the email. But it’s also technically accurate and the reason your boss might know is because Trustify will gladly tell them without any verification whatsoever. Trustify claim that “there are ways to hide the exposed details” in their original unsolicited email. Paradoxically, Trustify offers a commercial service to help you remove data from the web whilst also making it freely searchable to anyone thus demonstrating that in fact no, you cannot remove this sort of information because some idiot will always make it public.
I have a flooded inbox of people absolutely beside themselves because sites like this have “outed them” as Ashley Madison members regardless of whether they were actually there for an affair or someone else signed them up. All the legal ramblings of “just because someone was found in our system via a public search service doesn’t mean they signed up to AM themselves” don’t change the fact that a positive hit puts the individual under suspicion. I referenced many of these cases in that earlier post – there is a serious human impact from this event and profiteering like this makes the situation even worse. That Trustify actually go out of their way to recommend searching for other people is reprehensible:
This is not nuanced wording – the intention is to enable and indeed encourage spying on others which is why the first screen cap above says “Enter your email address (or the email address of your spouse)”. Or assumedly your work colleagues. Or your church congregation. Or your other family members. In fact they’re so desperate for you to check anyone, they even made a handy social button to tenable tweets like this (that link is a Twitter search):
I found my ex on Ashley Madison! You can search too http://t.co/xKR37Zm1yJ @trustifypi
— Jackie Okimoto (@Jackie_R_O) August 21, 2015 I found my friend on Ashley Madison! You can search too http://t.co/7pR7zjgRkv @trustifypi
— del (@del_gates) August 21, 2015 I found my ex on Ashley Madison! You can search too http://t.co/JDjBmhnYpm @trustifypi
— Debra Bennett (@BestDebbi) August 21, 2015 I found my friend on Ashley Madison! You can search too http://t.co/LA59xP0dAK @trustifypi
— Bobbi Garcia (@garcia_bobbi) August 20, 2015 Trustify has since removed the text about checking up on your spouse and has added a message about sending emails after the form on the page appears, but clearly there is still encouragement to search for other accounts. People will focus on the action they’re there to perform and won’t read additional text after that and even if they did, they’ll still do the check anyway because hey, there’s nothing to tie it back to them – it’s an anonymous publicly accessible service!
Other comments from thejournalizer go on to say:
Obviously fear was not something we want to be associated with this
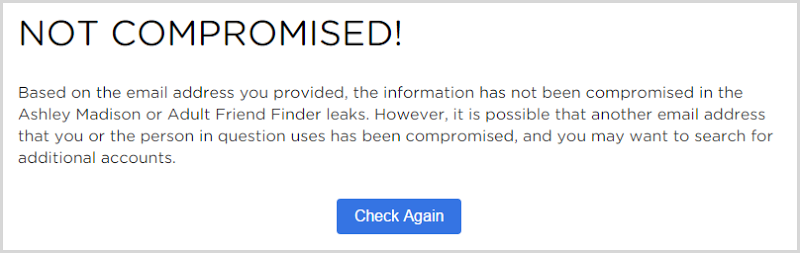
But then you browse around Trustify and get messages like this:
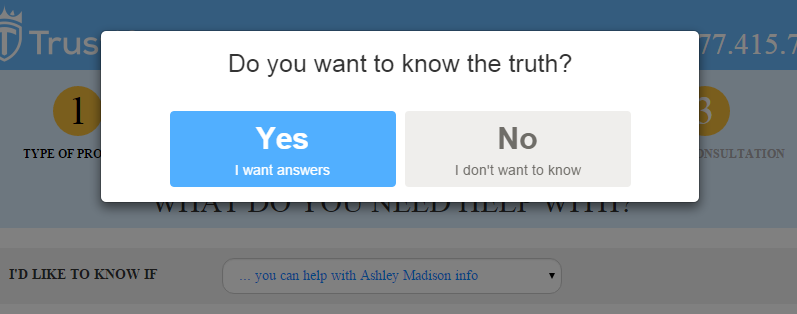
I almost expected to see “You can’t handle the truth!” after clicking on the negative! And again, this is in light of emailing people and warning them that their boss might know; if not fear, precisely what emotion were they expecting people to express upon seeing this?
In retrospect, the penny should have dropped a bit earlier. I had this question put to me a couple of days ago:
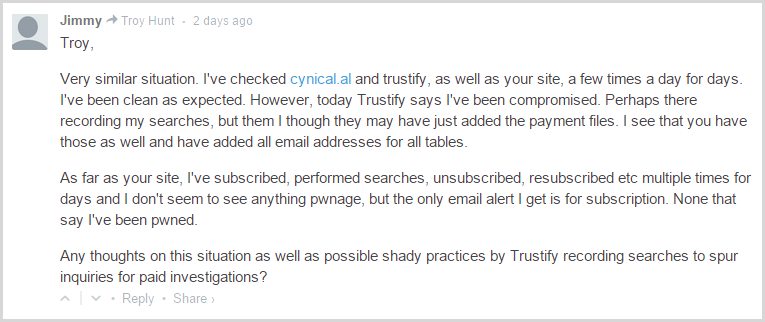
Some of this we can now confirm – Trustify is recording searches and spurring inquiries for paid investigations – but other aspects such as why they would later report an address as being compromised we can only speculate on based on what we know about the ethics of the company…
For anyone from Trustify reading this: take a step back from the immediate temptation to capitalise on the event and think for a moment what this actually means for individuals getting your emails. I understand the temptation to contact every hit searched for – it’s probably given you millions of opportunities to reach out to potential new customers – but you can still offer the service and ensure it’s only used in an ethical fashion. In fact I would applaud a method by which you verify the identity and make the person’s full data from Ashley Madison available to them; that would be a genuinely valuable service if done in a responsible fashion. It’s not difficult, you’re not going to upset “Legal” and it will only adversely impact those who shouldn’t be searching there in the first place. You’ve acknowledged that many people are directing a lot of negative attention towards Trustify in your Reddit AMA and it’s not hard to gauge the community sentiment from the comments there. You have the alibility to alleviate some of the pain the victims are feeling, stop adding to it.
Full disclosure: I started HIBP in 2013 and it provides the ability to search across about 220M records in 53 data breaches and another 18M records in 27k pastes. I do not charge for the public service, the only money I make from it is via donations which cover costs and coffee and the callback implementation for vetted commercial organisations. I don’t profit from searches or subscriptions and there is no financial incentive for me to drive traffic to HIBP rather than alternate search services. HIBP allows members of the public who can verify their email address to assess their Ashley Madison exposure for purely altruistic reasons.