You know what really surprised me about this whole WannaCry ransomware problem? No, not how quickly it spread. Not the breadth of organisations it took offline either and no, not even that so many of them hadn't applied a critical patch that landed a couple of months earlier. It was the reactions to this tweet that really surprised me:
Why is malware effective? Because of idiotic advice like this: "Stop Windows 10 from automatically updating your PC" https://t.co/cRygHYMPNh
— Troy Hunt (@troyhunt) May 13, 2017
When you position this article from a year ago next to the hundreds of thousands of machines that have just had their files encrypted, it's hard to conclude that it in any way constitutes good advice. I had the author of this post ping me and suggest that people should just manually update their things if they disabled Windows Update. That's fine in, say, a managed desktop environment such as many organisations run and let's be clear - disabling Windows Update isn't the issue in that situation because there are professionals managing the rollout of patches (with the obvious exception of the organisations that just got hit by WannaCry). But your average person is simply not going to keep on top of these things which is why auto-updaters are built into so many software products these days. Obviously they're in Windows, same with Mac OS and iOS, same with browsers like Chrome and Firefox and same again with the apps themselves on a device like your iPhone by virtue of the App Store automatically keeping them current.
Often, the updates these products deliver patch some pretty nasty security flaws. If you had any version of Windows since Vista running the default Windows Update, you would have had the critical Microsoft Security Bulletin known as "MS17-010" pushed down to your PC and automatically installed. Without doing a thing, when WannaCry came along almost 2 months later, the machine was protected because the exploit it targeted had already been patched. It's because of this essential protection provided by automatic updates that those advocating for disabling the process are being labelled the IT equivalents of anti-vaxxers and whilst I don't fully agree with real world analogies like this, you can certainly see where they're coming from. As with vaccinations, patches protect the host from nasty things that the vast majority of people simply don't understand.
This is how consumer software these days should be: self-updating with zero input required from the user. As soon as they're required to do something, it'll be neglected which is why Windows Update is so critical. Let's start there:
Leave your automatic updates on
The frustrating part of the debate that ensued after that tweet is not that people weren't proactive in protecting themselves, rather that they were proactively putting themselves at risk by disabling security features. Windows Update is the default position; you install the operating system (or receive it pre-installed from your hardware vendor of choice) and it looks like this:
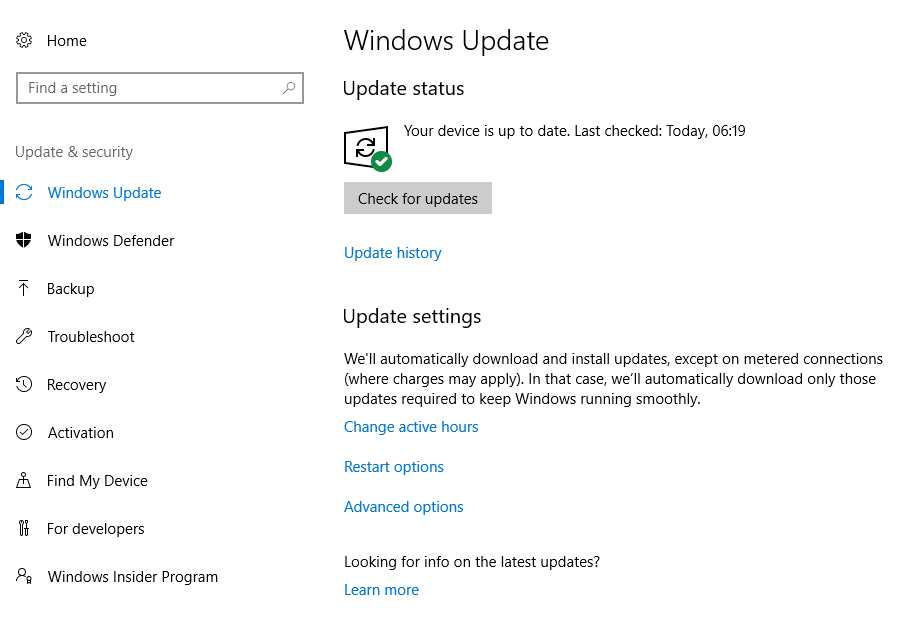
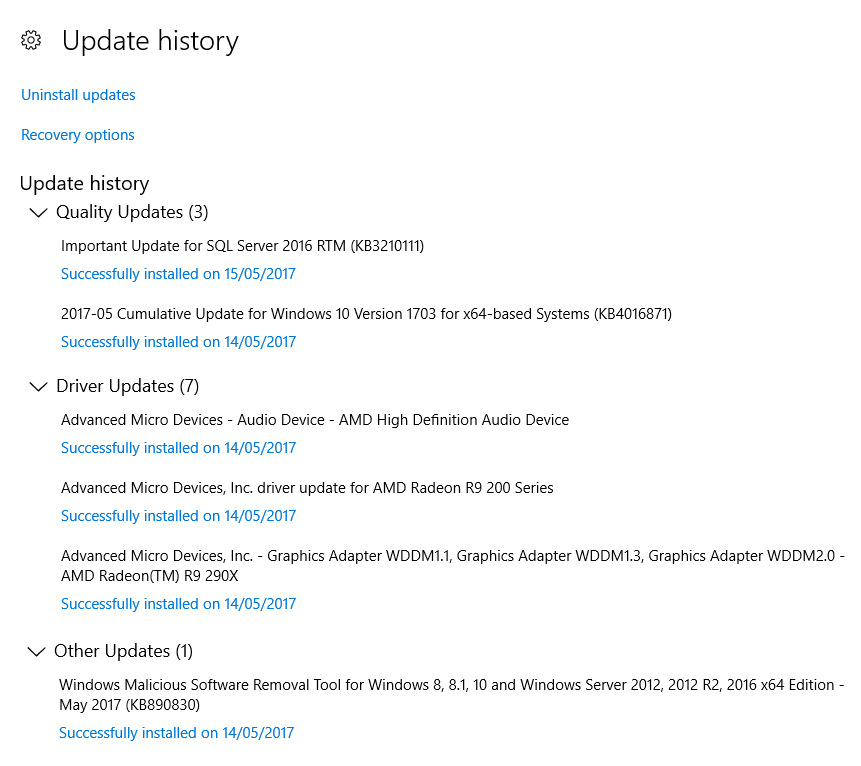
And then you go about your business. By pure coincidence, I rebuilt my desktop machine over the weekend and left Windows Update to do its thing which consequently meant getting a bunch of patches:
I start work early in the morning and often finish late which means I don't want things restarting on me while I'm busy so I customised my active hours:
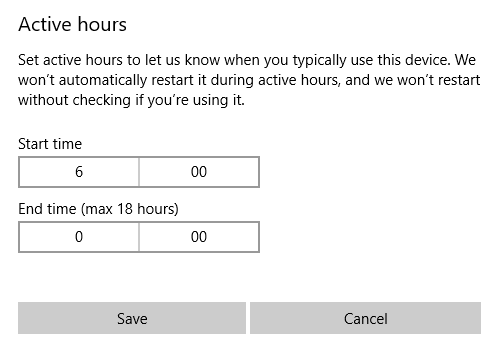
And there's a bunch of other configurability as well which I won't go into here. Point is that straight out of the box, updates are being applied and it's easy to minimise the adverse impact by virtue of defining those active hours. But this is not perfect - far from it - and believe me, I've felt the pain of Windows Update on many occasions so let's acknowledge that:
Sometimes, updates will annoy you
I've had Windows Update make me lose unsaved work. I've had it sitting there pending while waiting to rush out the door. I've had it install drivers that caused all manner of problems. I've had it change features so that they work differently and left me confused. I've had it consume bandwidth, eat up storage capacity and do any number of unexplainable things to my machines.
Those of us who've felt Windows Update-inflicted pain will all agree on this:
Microsoft needs to make Windows Update better.
Because let's face it, all of these things are fundamentally annoying. Some of them are even costly and if you haven't yet had an occasion where you've sworn at an update, you either haven't spent enough time with Windows or you're much more even-tempered than me. Microsoft needs to reduce the frequency of updates, reduce the occasions where it breaks things and reduce the times where updates happen at the most inconvenient times.
Now that has been improving over recent versions and certainly Win 10 has made many positive steps forward in this regard. But it's not iOS-slick yet; I'd love it if my Windows boxes updated as smoothly as my iThings. I can see why, of course: we're talking about Apple managing updates in an ecosystem where they control both hardware and software and have a very limited number of combinations of the two to worry about. The number of mixes and matches of Windows hardware and drivers is unfathomably large, and that's before you throw in all the various software packages that are distributed in all sorts of strange ways. It's a very complex ecosystem they're dealing with.
Regardless, it's important to acknowledge how frustrating the experience can be when stuff goes wrong. But right now, you need to decide what to do about it:
This is how it is, now make a decision
We agreed that Microsoft need to make this better, right? Cool, now what? I mean it's all well and good for some people to be unhappy with the way updates run today but what are you actually going to do about it? A number of people engaged in discussion after that tweet which was very, well, "enthusiastic" and that's fine, but what would they actually tell people to do?
Last year US-CERT wrote about ransomware and one of their recommendations was as follows:
Keep your operating system and software up-to-date with the latest patches. Vulnerable applications and operating systems are the target of most attacks. Ensuring these are patched with the latest updates greatly reduces the number of exploitable entry points available to an attacker.
And in the wake of WannaCry, Microsoft's President and Chief Legal Officer wrote about the need for urgent collective action:
This attack demonstrates the degree to which cybersecurity has become a shared responsibility between tech companies and customers. The fact that so many computers remained vulnerable two months after the release of a patch illustrates this aspect. As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems. Otherwise they’re literally fighting the problems of the present with tools from the past.
I doubt that even the most ardent opponents of my earlier tweet will disagree with either of the quotes above, so how are you going to achieve it if not by Windows Update? A portion of them will monitor the various patches and apply them as required, for example organisations with managed desktop environments (although again, as WannaCry demonstrated, there are some serious shortcomings in many orgs). Another portion will disable Windows Update and do nothing after which they might be ok. Maybe. For a while. They may also be WannaCry'd or Locky'd or whatever else but that's their prerogative and so long as they know the risk they were taking, I'm kinda ok with that. But your average Windows user doesn't know the risks and nor should they need to if they don't go turning fundamental security defences off!
So here's what I'll leave you with: there's no point chiming in about how you had a bad experience with an update once (or regularly), because other than vocalising those experiences to Microsoft and configuring updates within the scope of what Windows provides, you and I have no control over that (and no, I don't work for Microsoft). We've also just had a stark demonstration of what goes wrong when people don't patch so there's no point arguing about whether it may or may not be necessary. So what will you do? And perhaps more importantly, what will you advise other people to do?