Over the course of this week, I've been writing about "Fixing Data Breaches" which focuses on actionable steps that can be taken to reduce the prevalence and the impact of these incidents. I started out by talking about the value of education; let's do a better job of stopping these incidents from occurring in the first place by avoiding well-known coding and configuration flaws. I went on to data ownership and minimisation where I talked about giving people back control of their data and collecting less of it in the first place. And then yesterday, I encouraged people to make disclosure easier because there are way too many cases where serious issues go unreported.
Today's post extends on yesterday's but I wanted to break it out into a discrete piece and come at it from a different angle. Bug bounties have a really interesting way of changing the economics of security flaws and reversing the outcome from one where companies and customers lose, to promoting one where everyone wins. Let's explore that further.
The Mechanics of a Bug Bounty
The term is probably familiar to many of you so I won't dwell on it here, but I'd be remiss to assume that everyone understands the mechanics. Here's a brief description of the function of a bug bounty:
A bug bounty is a program offered by an organisation which incentivises people to identify and report bugs in their system. Bug hunters who discover security flaws are rewarded with anything from a mention on the company's website (Tesla has a security researchers hall of fame) to a t-shirt (Informatica will give you a t-shirt and a mention on their hall of fame!), to serious amounts of cash (Apple will pay up to $200k). The program is often scoped to certain assets owned by the company and rewards are tailored based on the value of the finding; PayPal has a bounty payments range of $50 to $10k and as you can imagine, something like a cookie without an HttpOnly attribute is in a different realm to a SQL injection flaw.
The main takeaway here is that a bounty is a legal construct which incentivises people to identify and report flaws. Let's move on and talk about why this makes a lot of sense when it comes to fixing data breaches.
The Economics of Breaches and Bug Bounties
I want to start with the financial incentives behind data breaches because this will help put things into economic terms. When the LinkedIn data breach from 2012 finally surfaced in May 2016, it appeared for sale on a (now defunct) dark web marketplace called The Real Deal. It was being sold for 5 Bitcoins:
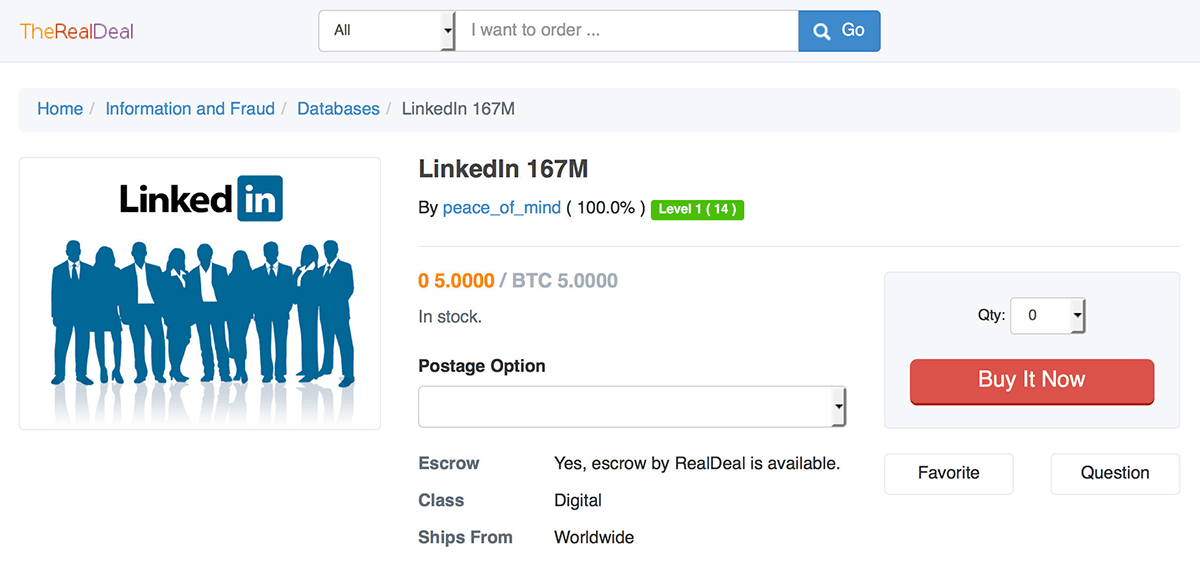
That's over US$80k in today's money but back then, it was only a couple of grand (which actually, seems like pretty good value for 167 million accounts and passwords stored as unsalted SHA1 hashes). The seller then sold it multiple times over before it leaked into the public domain and became commercially worthless.
You can see why the seller put the data on the market - there was a clear financial upside. But s/he also took significant risks in doing so and according to the news just a couple of months ago, an individual linked to the breach has been arrested in Prague.
Let's consider how the LinkedIn breach would have played out differently had there been a bug bounty in place. Firstly, when the individual who originally located the LinkedIn vulnerability came across that flaw in their system, they would have had an avenue for easy disclosure. To the point made in yesterday's post, it means a readily discoverable channel to communicate the flaw to LinkedIn without the fears I raised in that post.
Secondly, they would have had an alternate commercialisation model available which didn't involve breaking the law. If their motivation wasn't at all altruistic and all they wanted to do was cash in, they could have done so legally without spreading 167 million records (including mine!) across the internet. Now of course were that the case (the person being motivated by money), LinkedIn would also need to "meet the market" and pay an amount which justified disclosure to them rather than cashing in other ways. That $200k Apple bounty I just mentioned has come under fire because there are other parties that will pay up to $500k for the same thing. But there's one other angle to this...
Finally, both the legalities and ethics of reporting via a bug bounty would have been at a polar opposite to the way the LinkedIn situation ended up panning out. There'd be no fear of legal reprisals and no moral dilemma regarding the impact of this person's actions on other people. These are not always going to be sufficiently attractive outcomes to sway people in favour of disclosing via a bug bounty, but they add that much more weight to the ethical side of the scale that it would inevitably factor into the decision process that many people go through.
But bounties do much more than just incentivise people who find vulnerabilities to do the right thing, they have another really important outcome too. Let's explore that next.
The Economics of Bug Hunters
As the popularity of bug bounties has grown, there's been an increasing number of people who've carved out a living from finding and reporting security vulnerabilities. One notable story is that of 21-year old Nathaniel Wakelam, an Aussie bloke earning $250k a year hunting bugs. Now that's good money by any reasonable standard, let alone when you're 21 years old and as the story explains, this is just from working out of a coffee shop.
People like Nathaniel have this down to a fine art; hunting bugs is a process they run through over and over again, refining their art and reapplying it across all manner of different organisations offering bounties. For them, a site with a bug bounty is just another potential revenue stream they can tap into by applying their craft and seeing what pops up. They're drawn to sites with bounties because that's how they make a living.
Bug bounties increase the number of ethical parties looking for flaws in systems and in turn, reduces the number of vulnerabilities that would otherwise be targeted by malicious parties.
Of course, not everyone earns hundreds of thousands of dollars by probing away at other people's systems. Many bug hunters are doing it part time either for extra cash or simply because they love the challenge. So many of the data breaches people send me aren't because a criminal set out with an ROI in mind, they're because a kid (or a young adult) was curious so they started poking around.
Another interesting dimension to this is that most bug bounties (usually) have no geographical boundaries which means the ROI for the bug hunter can be enormously attractive. Whilst I was at a conference in Switzerland last year, I met a lovely bloke from Africa who was heavily involved in bug hunting. Consider what the "return" component of the ROI is for someone living in a market where the average income is a fraction of that in the countries many of these services are based in; this makes bounties enormously attractive and gets precisely the eyes you want looking at your security things. Bounties are a great leveller in terms of providing opportunity to all.
But as much as bug bounties have their supporters, not everyone sees them as a win-win so let's touch quickly on that.
But Doesn't This Mean Bad Dudes Will Probe our Systems?
When I run workshops, at the end of the second day I like to talk about automating security. This includes dynamic and static analysis, building processes into continuous integration environments and... bug bounties. The bounties fit logically into this section of the workshop for the very reason highlighted in bold a few paras up - they delegate out work to other parties who take on the responsibility of identifying bugs on your behalf.
However, I often see pensive eyes staring back and when I start to probe as to why, the same answer always comes back:
If we run a bug bounty, doesn't this mean we'll become a target and people will attempt to start hacking us?
Well, I've got bad news for you guys, you're already getting free penetration tests every day anyway, you're just not getting told of the results! The simple reality is that anyone who puts anything on the web will observe automated attacks that begin mere minutes after going online. Attacks are going to happen whether you have a bounty or not.
Bug Bounties Are Now Mainstream and Are Expanding Rapidly
I touched on a few organisations that presently run bounties earlier on, but the list goes well beyond those few. You can pick all sorts of verticals today that have companies actively engaged in bounties. Western Union has a bounty. Fitbit has a bounty. Tesla has a bounty. These are not niche, tech-centric companies, they're out there in the mainstream.
Then there's bounties run by the government. Singapore's ministry of defence just announced a bounty program and The Pentagon ran one that begun last year and has so far identified "thousands of bugs". These programs tend to be more tightly controlled (the Singapore government invited specific bug hunters), and given the nature of the organisations you can see why. Still, the core principles of a bug bounty remain.
Bounties are expanding at such a rate that there are companies springing up dedicated to helping organisations run them in a bug-bounty-as-a-service fashion. One of the most notable is Bugcrowd, started by fellow Aussie Casey Ellis and now operating very successfully in the US. For companies seeing the light of bug bounty value but not wanting to run the program themselves (which is going to be most of them), a service like Bugcrowd makes a heap of sense.
On that last point, I don't want to trivialise what's involved in running a bounty. If your average company stands up today and openly invites the masses to start testing their things, there's a fair chance it's going to quickly turn into a nightmare. There'll be a heap of low-hanging vulnerabilities found, a flood of reports and a subsequent nightmare triaging them all. This is why services like Bugcrowd's exist because it's not a trivial thing and I don't want to imply that. But it is a thing worth doing, it just takes some planning.
Summary
When you think about bug bounties in pure economic terms, they make perfect sense. They disrupt the traditional inclination to withhold information and flip that on its head such that people are incentivised to disclose it instead. Nobody "won" in the LinkedIn situation; it would have cost the company dearly to deal with it, millions of us had our personal data exposed and the guy involved is now facing extradition to the US where he will likely face a future with very few options in life.
Frankly, the greatest barrier I see to organisations implementing bounties is a negative perception towards folks outside of their control probing away at their things. We need to get over this; the entire theme of this series has been about how we can better deal with the fallout when precisely this happens anyway - unauthorised parties getting into our things - and incentivising people to do the right thing by way of bug bounties is an essential part of that.