Try publishing something to the internet - anything - and see how it long it takes before something nasty is probing away at it. Brand new website, new domain and it's mere hours (if not minutes) before requests for wp-admin are in the logs. Yes, I know it's not a Wordpress site but that doesn't matter, the bots don't care. But that's just indiscriminate scanning, nothing personal; how about deliberate and concerted attacks more specifically designed to get into your things? As the value of what you have increases, so do the attacks and there's absolutely nothing you can do about it. There's a lot you can do in terms of defences, but nothing you can do to stop randoms on the internet having a red hot go at breaking into your things.
This is why the discussion around bug bounties confounds me because every time I raise them as being a rather good thing for your security posture, I inevitably get a response along these lines:
But doesn't a bug bounty mean hackers will try and break into our things?
I hate to break it to you, but that's business as usual whether you have a bounty program or not, the only difference is going to be what they do if they successfully get in. That's oversimplifying things, of course, but to me that's always been a cornerstone of why bug bounties make so much sense: they change the ROI of bugs such that it incentivises people of all ethical positions to disclose them to the organisation involved rather than run amuck with them. Plus, it draws people to the site and encourages them to seek out vulnerabilities thus improving the overall security posture. Which brings me to this:
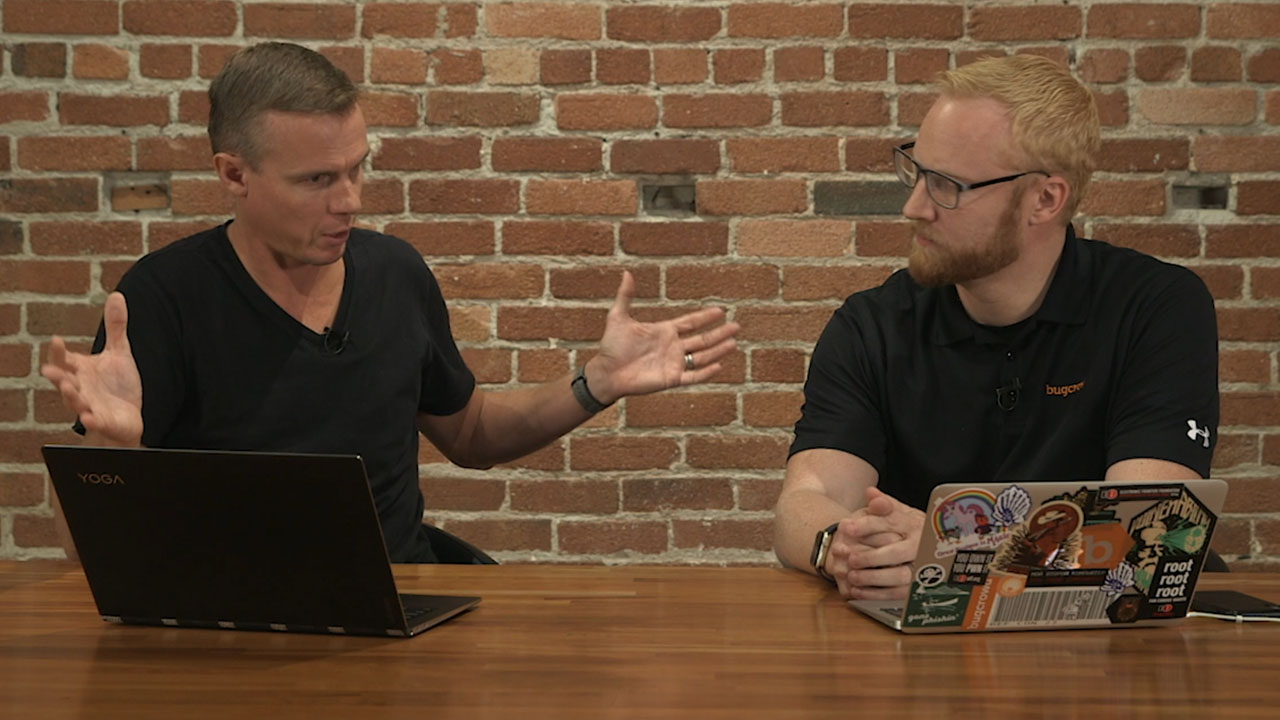
I'm sitting with Casey Ellis in a studio in San Franciso recording a Pluralsight course per the title of this blog post. Casey is the founder of Bugcrowd and they help companies ranging from MasterCard to NETGEAR to Western Union run managed bug bounty programs. Casey and I have been mates for about 5 years now, in fact I went back and checked my email and it was Jan 2013 when we first caught up over beers in Sydney and he shared his vision for Bugcrowd. That vision ultimately got him funded and led him to Silicon Valley. When we caught up to do this course, Bugcrowd had just received another $26M, and that's on top of the $23M that had already been invested in the company. Whilst this course isn't specifically about Bugcrowd, I wanted to share that background because I couldn't think of a better person in the world to have recorded this course with.
So, getting onto the course, I really wanted to tackle the barriers organisations typically see to implementing a bug bounty program; does it really put them at greater risk? How do you price bugs? How do you decide on the scope? When's the right time to run one? Understandably, people have many questions about running a bounty and I reckon we've done a great job of addressing them here. It's a 48 minute "Play by Play" course so it's just Casey and I sitting around chatting (along with visuals from his screen), so it's easily consumable material. This is also the first of 2 courses we recorded with "Bug Bounties for Researchers" still to go live. That one will focus on individuals who want to get involved in bug hunting so it comes at things from quite a different angle.
Incidentally, my favourite password manager 1Password has a $100k top reward on Bugcrowd. They're so confident in the security of their solution and the value of a successful exploit is so high that they'll reward you very handsomely if you manage to break into a 1Password vault. Given the value of my own things I put in their care, I'm pretty happy to see that!
Bug Bounties for Companies is now live!