If you're here reading this then it probably won't come as a big surprise but brace yourself anyway - we have a security problem. Yes, yes, I know, it's all very terrifying and not a day goes by where someone isn't getting cyber-something'd. As best I can tell from the news, it's pretty much all to do with guys in hoodies sitting at green screens pwning all our things. I'm quite sure that's the case, I even did a quick check on Google to confirm:

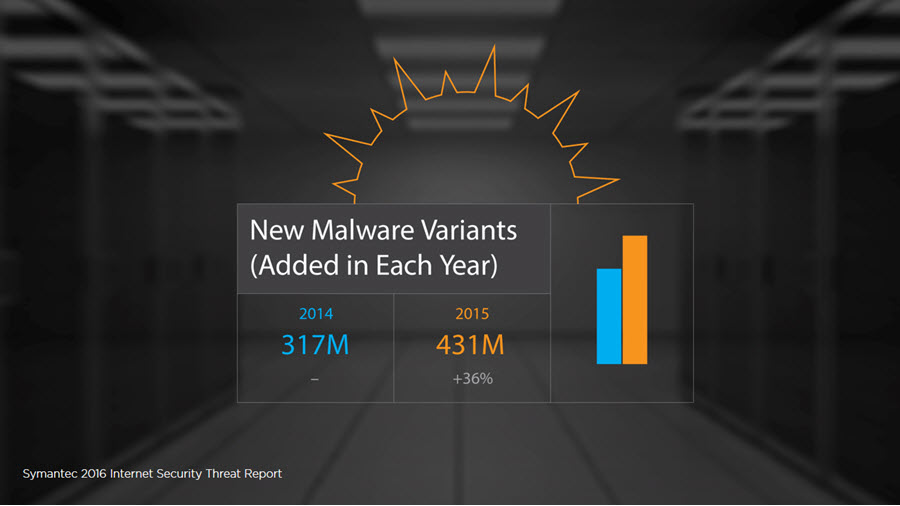
I talk about these crazy hacker perceptions in the intro of my new Pluralsight course and despite the sensationalist and inaccurate imagery in the reporting, security genuinely is a big problem. In my view, much of it has to do with many fundamental misunderstandings, even amongst those who are more technically inclined. I wanted to make a course that challenged many of the views people hold about security and took them to places that, well, might make them feel a little bit uncomfortable. For example, people run anti-virus with the expectation that it will do precisely what the name suggests, yet in the second module when I delve into The Soft Centre Within Our Networks, it becomes pretty evident that traditional signature-based AV is losing the battle:
Speaking of feeling uncomfortable, I love opportunities to turn conventional wisdom on its head so in the third module on The Security Lies We Tell Ourselves, I talk about what's safe to browse and what's not:
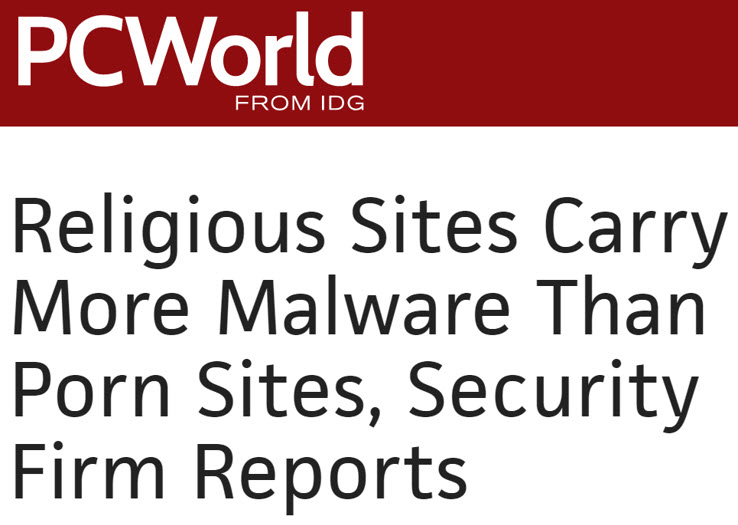
Now I'm not saying that when you next kick back for a bit of lazy web surfing this should necessarily influence where you browse to, but there are some genuinely interesting insights in here. When Symantec prepared this report a few years ago, they identified a number of factors that made porn a safer bet than religion, including the fact that the former has a monetisation strategy that's heavily dependent on them keeping their site safe. You're (probably) not going to change religion if you get a virus from your local church's website, but you may choose another location for your adult entertainment if the same thing happens there. This then leads us into discussions about topics such as malware distribution via ad networks that can happen on seemingly innocuous websites which then turns into a discussion on the role of ad blockers.
The fourth module talks about The Problems (and Solutions) with Mobile Devices and it gets us into important issues such as gummi bears:

There's context here, of course, and it has to do with biometrics and the assertion that they're "unsafe" due to the ability to create gelatin moulds of fingers thus circumventing what is becoming an increasingly popular security control on mobile devices. This was demonstrated as far back as 2002 (probably further) and biometric-naysayers will argue that it proves this mechanism of identification is "insecure". But when you look at what's actually involved in a workable attack and you think about your threat actors - which are almost certainly the folks in the image above - the reality starts to look a lot different. There's a very pragmatic discussion to be had around all this and I cover it pretty holistically in the course.
Moving onto the fifth module and it's What People Just Don't Understand About the Web. For example, websites in the EU are doing a good job of scaring the bejesus out of anyone with cookies enabled by throwing big warnings around about tracking. Yet you don't need cookies to be tracked and I love showing people amiunique.org just to make a point of it:
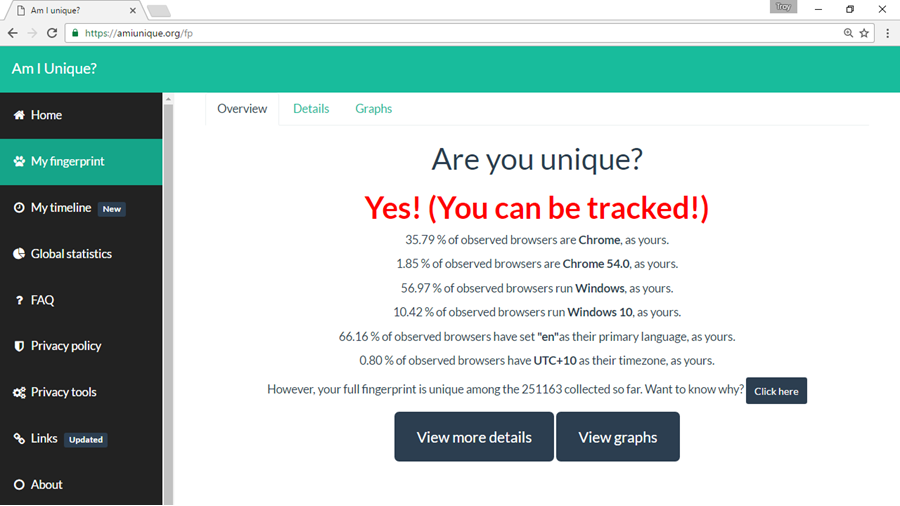
Go and give it a go and you'll almost certainly find that just as your mother told you, you are indeed a unique snowflake. Disable your cookies, remove your plugins and turn off your JavaScript and you can still easily be tracked. Now how 'bout removing those inane cookie warnings, Europe?
And finally, in the sixth and final module, it's The Painful Truths About Passwords and Authentication. I love this module, because I get to talk about how badly people screw up 2FA:
How to NOT implement #2factor #authentication http://151.32.95.155/index.html #2FA #epicfail pic.twitter.com/Ql9JF7Mkx9
— Davide Paltrinieri (@davide_paltri) December 15, 2015
Yes, that is what it looks like. Reckon that's nuts? How about not just pointing a webcam at the token (you know, the thing you're meant to have which is what makes it a second factor in the first place!) but also writing a blog post about how to do it including OCR'ing the PIN. I've got a long and prosperous career ahead of me at this rate...
I wanted this course to highlight security in ways that many people don't usually think about it. I wanted it to span both technical and non-technical audiences and I really wanted it to be an enjoyable course to watch. It comes in at 2 hours and 17 minutes and we've positioned it as a "Big Picture" course so it covers a lot (far more than just the bits I've highlighted here) but it doesn't go too deep. I've had this one in planning for a long time and it took a lot of work to get the balance just right so I'm really hoping that it's well-received.
The Information Security Big Picture is now live on Pluralsight!