Two of the things you'll have found me most frequently writing about on this blog are "cloud" and "security". Whilst the latter seems to have been what I've gravitated towards most in recent years, the former is something I'm very heavily involved in, particularly with my work on Have I been pwned (HIBP). I'm enormously happy to see the very last course in the Ethical Hacking series I've been building out with Pluralsight now complete with the 8th and final one being Ethical Hacking: Cloud Computing. Overwhelmingly excited. Ecstatic!
I'll come back to why I'm so happy that the entire thing has now been wrapped up, but let me start with my favourite cloud question of all:
Is "the cloud" secure?
I love this question for a couple of reasons. Firstly, it implies that there is "a cloud", as though it is this one thing that everyone uses. Many of my readers will immediately see the flaw in the logic here; the cloud I run HIBP on is different to the cloud my iPhone backs up to which is different to the cloud you're reading this blog on (which is also served through a cloud proxy service - CloudFlare). They're very different cloud services serving very different purposes and presenting very different risk profiles.
But most of all, I love this question due to one simple fact: it's a terrible question. I love it being a terrible question because it allows us to have a discussion about what people asking it really mean. This question is often asked by people considering a move to cloud computing and these days I answer it by telling a story:
A couple of years ago in a previous career, I was called over to Beijing to help sort out some issues with a piece of software. It was a critical application for the organisation; a halo project in a behemoth multinational in the fastest growing region in the world. I spent several days with the team working on all the usual sorts of issues that large software projects face. Not security related in this case, but performance, maintainability, release management and so on and so forth. As we wrapped up with a little time to spare, one of the girls in the team asked about Azure. I did the usual dog and pony show (essentially a very compressed version of Modernizing Your Websites with Azure Platform as a Service) after which I got that exact question:
Is "the cloud" secure?
This was a great opportunity: "I don't think you're asking the right question", I replied, "Let me give you a demonstration". Now this all happened very quickly so let me summarise it in point form:
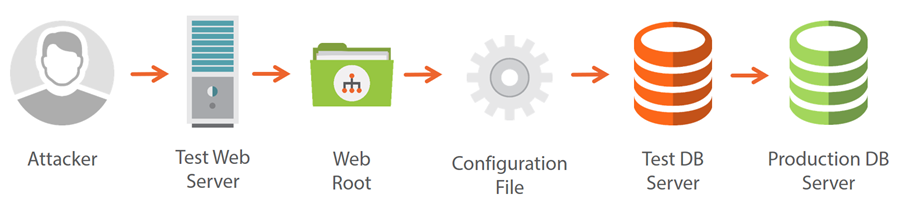
- I went to the test version of the application I was there to consult on
- I took the URL and resolved it to a host name
- I then browsed over to that host via Windows Explorer
- I discovered a shared folder that pointed to the web root of the project
- There were no access controls on the folder (full control to everyone)
- It was an ASP.NET application which contained a web.config file
- The web.config had an unencrypted connection string using a SQL login
- The SQL login used the sa account...
- Now I had full access to the test database server
- The test database server had a linked server to production
- The account the linked server used had full control over the production database
This was a 5-minute exercise and anyone with half a clue could have easily reproduced the same process very quickly. It was literally this simple:
I use this example in the first module of the course because it helps set the tone of the discussion we should be having about cloud security and that's not talking about it like it's some secure / insecure boolean state, rather that it's different. Rather than asking if the cloud is secure, here's what people should be asking instead:
How does cloud computing change the security posture of what we're doing now?
There are many aspects of a well-executed cloud strategy that would totally change the security landscape of the situation I described above. By the same token, it could have been done properly on-premise as well but what was lacking was competency in those administering the environment. You go to the cloud and you start to get choices about how much administration you delegate back to the provider by virtue of IaaS, PaaS and SaaS offerings. If I had architectural control over this particular system, I would have thrown it all into PaaS and not given anyone the ability to open up shared folders or create linked servers or do any number of things that seriously jeopardised the security position of this project.
The fact that cloud computing leads to so many new discussions about security is really the point in terms of looking at how things change. Because of that, I wanted to create a really balanced course that looks at both the strengths and weaknesses of the cloud. Here's what's in there:
- Cloud Computing Concepts
- Organizational Security Considerations
- Cloud Computing Risks
- Cloud Computing Security Strengths
- Hardening the Cloud
Balance and objectivity is really important and didn't want to go into this all "ra ra ra, cloud is awesome, cloud all the things". Because of that, I talk about the risk of things like having your administration portal compromised - that's a sure way to mess your day up very quickly (and probably much worse). Or how about the risk of an EDoS attack or "Economic Denial of Sustainability". A great example of this is that you don't normally pay for ingress data in a cloud service (for example, outbound requests from a VPS), but you do pay for egress (for example, requests to a cloud website). So the attacker hammers your site from another service loading the largest content they can as fast as they can. Your site stays up, but suddenly your costs go nuts because cloud computing is a measured service - you pay for what you use.
Obviously three hours of content goes into a lot more detail than that across a much broader range of cloud security topics, but you get the idea. I really hope this course helps people learn how to think about security in the cloud. It's not always a more secure or even less secure proposition rather as I keep saying, it's just different.
This wraps up everything I was slated to produce for the Ethical Hacking series, a journey I started way back in March last year. That may not seem like a long time, but a huge amount of water has gone under the bridge for me personally since then. I'm just waiting on my co-author Dale Meredith to finish his very last course and I'll write something more general about the Ethical Hacking series and indeed about the CEH certification in general once the whole package is there for everyone.
I hope you enjoy watching this course as much as I enjoyed finishing the series - Ethical Hacking: Cloud Computing is now live!