Time and time again, I get emails and DMs from people that effectively boil down to this:
Hey, that paste that just appeared in Have I Been Pwned is from Spotify, looks like they've had a data breach
Many years ago, I introduced the concept of pastes to HIBP and what they essentially boil down to is monitoring Pastebin and a bunch of other services for when a trove of email addresses is dumped online. Very often, those addresses are accompanied by other personal information such as passwords. When an HIBP subscriber's address appears in one of these incidents, they get an automated notification and often, it seems, they then reach out to me.
Here's a perfect example of what I'm talking about, this one eventually triggering an email to me just last week:
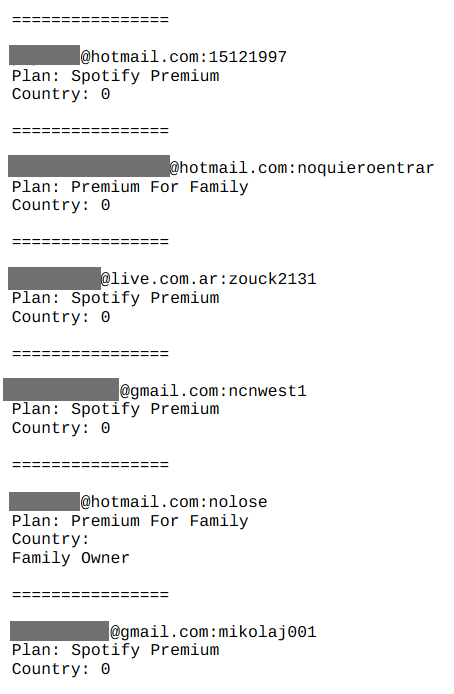
Let's imagine you're the first person on the list; you get a notification from HIBP, you check out the paste and see your Hotmail account listed there alongside your Spotify password and the plan you're subscribed to. Clearly a Spotify breach, right?
No, and the passwords are the very first thing that starts to give it all away. Just looking at them, they're obviously terrible, but plugging the first one into Pwned Passwords give you a sense of just how terrible it is:
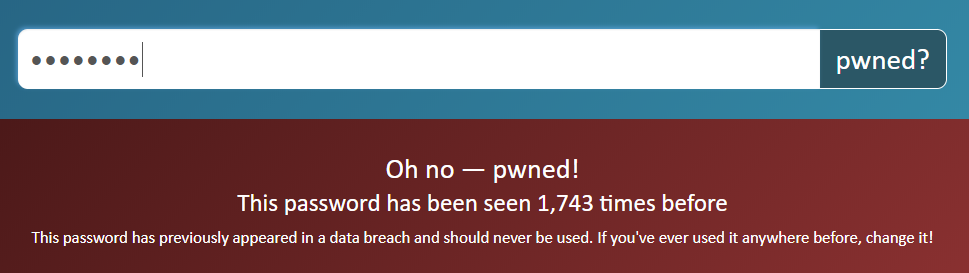
They may not all be that bad (the next one in the list has only been seen twice), but the point is that it's a password that's clearly been seen before and were I to dig back into the source data, there's a good chance it's been seen in a breach alongside that email address too. Then there's the fact that the password is in plain text and I don't know precisely how Spotify store their passwords, but it'd be a very safe bet that by now it's a decent modern-day hashing algorithm. If they had a breach then yes, hashes may be cracked, but that's not what's happening here.
We're simply seeing the successful result of credential stuffing attacks. Regular readers will appreciate the mechanics of this already but all those who I point here for whom this is new, this attack simply takes exposed credentials from a data breach and tries them on another site. The attack is simple but effective due to the prevalence of password reuse. If you were using the same password on LinkedIn when they had their data breach as you are on Spotify today and someone grabbed that password from the breach and tried it on Spotify, you can see the problem. That's it, job done, they're into your account.
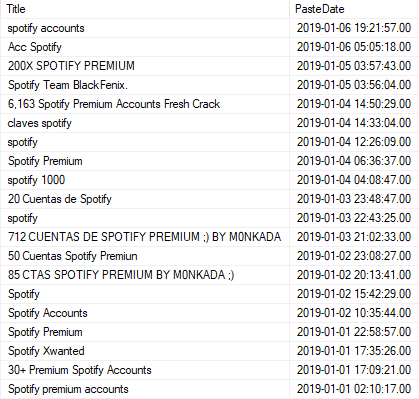
Spotify "breaches" like this are enormously common. I just went and looked at the pastes HIBP has collected since the clock ticked over to 2019 and found 20 of them already:
Digging further, I found over a thousand pastes with "Spotify" in the title. These are often removed by Pastebin pretty quickly but looking through some that remain, it's precisely the same pattern as the earlier example. I grabbed a random email address out of one of them and checked it on HIBP:
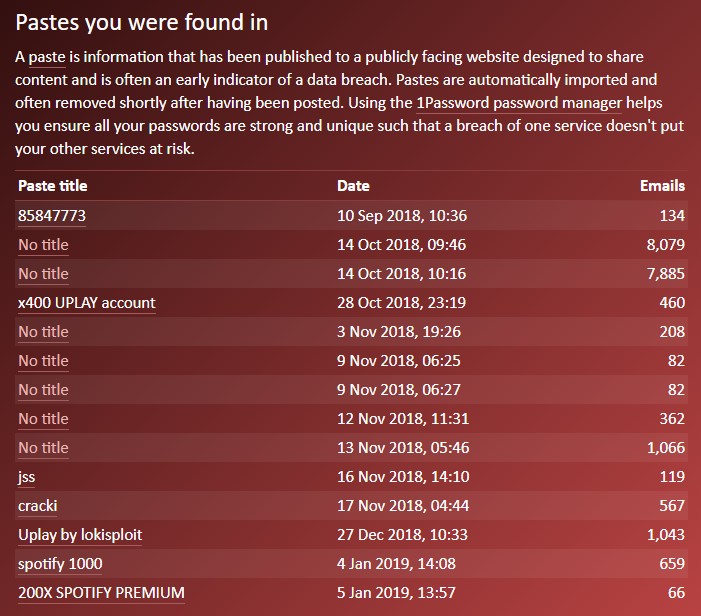
The same address appears over and over in pastes and each time, the same password appears alongside it. Picking one from the list above that hasn't yet been removed shows a page full of examples like this (with a password Pwned Passwords has seen 4 times before):
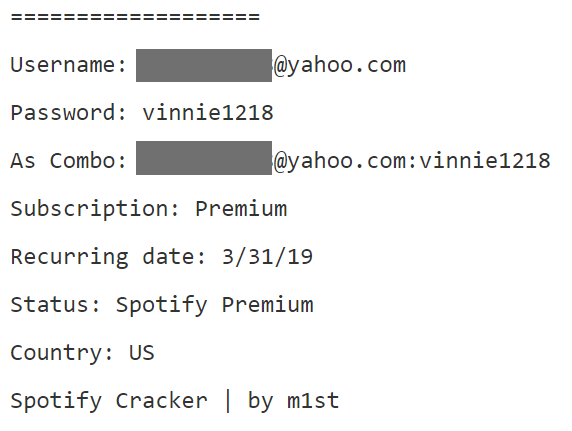
This one is interesting for a couple of reasons and the first is the use of the term "combo". I've written about combo lists before and they're essentially combinations of email addresses and passwords used to test against services in credential stuffing attacks. Thousands. Millions. Billions of them, in some cases. The second interesting observation in that image is the "Spotify Cracker" reference. The first Google result for the term shows a popular cracking forum with the following image (password seen 447 times in Pwned Passwords):
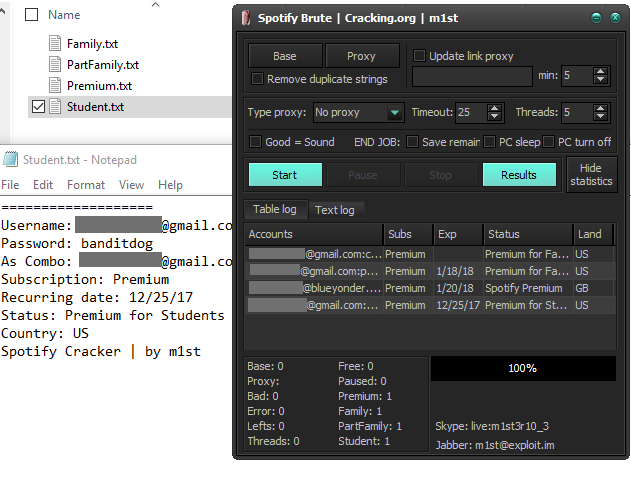
This is a tool for breaking into Spotify accounts I wouldn't normally link through to content of that type, but context is important. For people wondering why they're getting alerts from HIBP because their Spotify account is in a paste somewhere, have a flick through some of those pages. 61 of them at the time of writing, each with 20 posts thanking the OP for their work in order to get access to the tool. So what does it do? Have a quick watch of this:
It's a slightly different piece of software based on what's visible, but the objective is the same and the premise is simple: download the tool, pass in the combo list then let it run. Credentials from the list are then tested against Spotify (yes, security friends, there's a very good question to be asked here as to why this is still possible...) and results appear on the screen.
Now, this isn't to say that someone who finds their Spotify account on one of these lists shouldn't worry because it wasn't a breach per se. Instead, they need to look inwardly and adjust their own security practices instead. Get a password manager (8 years on and I still use 1Password every day), create strong and unique passwords on every account and enable 2-factor authentication where available. Well, except that there's still no 2FA support on Spotify so just enable it on every other service that supports it (and most big ones do these days).
And why would someone "hack" (I use the term loosely because they literally logged in with the correct username and password) Spotify accounts? The obvious answer is that they have a monetary value, but I also posit that it's very often just curiosity driving this behaviour. Take a look at a video such as this SQL injection tutorial; I've used it in talks before to illustrate the randomness of attacks as well as the sophistication of those behind many of them. Is the person in this video an evil cyber hacker hell-bent on causing chaos, or just a curious kid whose moral compass is yet to be properly calibrated? That may not make Spotify users feel any better about the end result, but it's important context for this post.
In doing a bit of searching for this piece I found heaps of results for "spotify data breach" that led to discussions highlighting what I've covered above. For example, this one from August on the Spotify community site where the original post begins with:
Someone had access to my pasword [sic] (which is totally unbreakable and diferent [sic] from the one i use in other accounts)
I don't know what their password was, but I do know that I've had dozens of discussions with people making precisely the same claims only to discover "their" password is in Pwned Passwords a few hundred times! Or they entered it into a phishing site somewhere. If we apply Occam's Razor to this (the simplest solution is the most likely one), the password was compromised. I want to illustrate this point via the following Tweet:
For ref, here are the details on my 1Password entry for Pinterest. Definitely the strong, unique one I showed in my tweet. pic.twitter.com/d3sSR8PCu1
— Scott Helme (@Scott_Helme) December 9, 2017
This is Scott Helme, a world-renowned security researcher who understands these concepts as well as anyone I can imagine. This tweet is part of a broader discussion where his Pinterest account was logged into by an unknown party and per the image above, Scott was convinced his password was both strong and unique. A couple of hours later, Scott's view is, well, somewhat "different":
Just goes to show, it's sometimes easy to miss these things! I'm now wondering how many other old accounts I have lurking around out there... ? 5/5
— Scott Helme (@Scott_Helme) December 10, 2017
I spoke to Scott about this incident again whilst writing this post and we both reflected on just how easy it is to have issues like this, even you're convinced your security is spot on. It's precedents like this which cause me to pause and question every strongly made claim of personal security prowess in the wake of examples such as the Spotify community one above.
Reading through that thread only reinforces the view that this was a simple account takeover issue and not a sophisticated hack. For example, this comment:
It's such a shame to see Spotify blaming its users for getting hacked instead of fixing the problem. Got my playlists deleted and the hacker created a playlist called "Get Hacked".
Imagine you're a hacker - a real one with the capabilities to break into a company with hundreds of millions of users and worth billions of dollars - what are you going to do? Are you just going to mess with people's playlists "for the lulz"? No, at the very least you're going to cash in on their public bug bounty or if you're really the malicious type, you're going to monetise their users in a much more surreptitious fashion.
Scroll down a little further and someone is referencing HIBP as "proof" of a hack. Here's what happened to the guy's account:
I got a notification from haveibeenpwned.com and did nothing about it until some random kept playing weird music on a device I did not recognize while I was trying to listen on my normal device. It was annoying, I kept getting pulled out of my song because we started battling for control of what device and what song the audio was to be heard on. I started playing really loud and obnoxious noise music for the hacker while I changed my password.
Now again, let's apply Occam's Razor: is this an elite hacker who's discovered some previously unknown zero-day vulnerability, or someone who's exploited the victim's password and then simply has a different taste in music?
The community thread references a paste titled "Más de 300 cuentas premium de Spotify" ("More than 300 Spotify premium accounts") which has since been deleted from Pastebin (and HIBP doesn't save the contents beyond just the email addresses). But 4 days earlier there was a paste titled "Más de 50 cuentas premium de spotify" which still stands today and its content lines up very closely with the others discussed above; it's simply the output of another automated tool exploiting weak credentials.
I'll end on one final point because if I don't, it'll come through in the comments anyway: online security is a shared responsibility. Some people are quick to play the "victim blaming" card when I write about incidents that can be traced back to weak security practices. Clearly, that's not causing me to sugar-coat the root cause of these incidents but that said (and I touched on this earlier), this is prevalent enough that Spotify also needs to look internally at why this is still occurring. Their job is to stop this form of attack at the platform level and our job as users of the service is to protect our accounts via some basic security practices.
So no, Spotify wasn't hacked, they just allowed malicious parties to log in with other people's poor passwords.