I started doing these retrospectives 3 years ago in my first year of independence. I reckon they're a good thing for everyone to do if not in written form then at least mentally to look back on your achievements of the year. They're a great way of reflecting on success (and indeed, on failures) and they also help explain why we all feel so damn tired by the end of the year!
Here's my 2018 highlights, starting with travel:
Travel
"Oh yeah, I'm totally gonna travel less this year" - me every single year
In reality, my travel ended up looking like this:

That's the same number as last year, 4 more days and another 8,000km. On the other hand, it's 12 less cities and 1 less country and the main reason for that is I've been trying to cram less into trips. I've also been travelling with family far more so whilst those 140 days equate to 38% of my year, there were 14 days in Hawaii, 10 days at the Aussie snow, 11 days in Texas and 17 days in Canada where I wasn't flying solo. That's 52 days where it wasn't just a lonely slog so I'm pretty happy about that.
Flight wise, App in the Air captured things in a nice visual fashion:
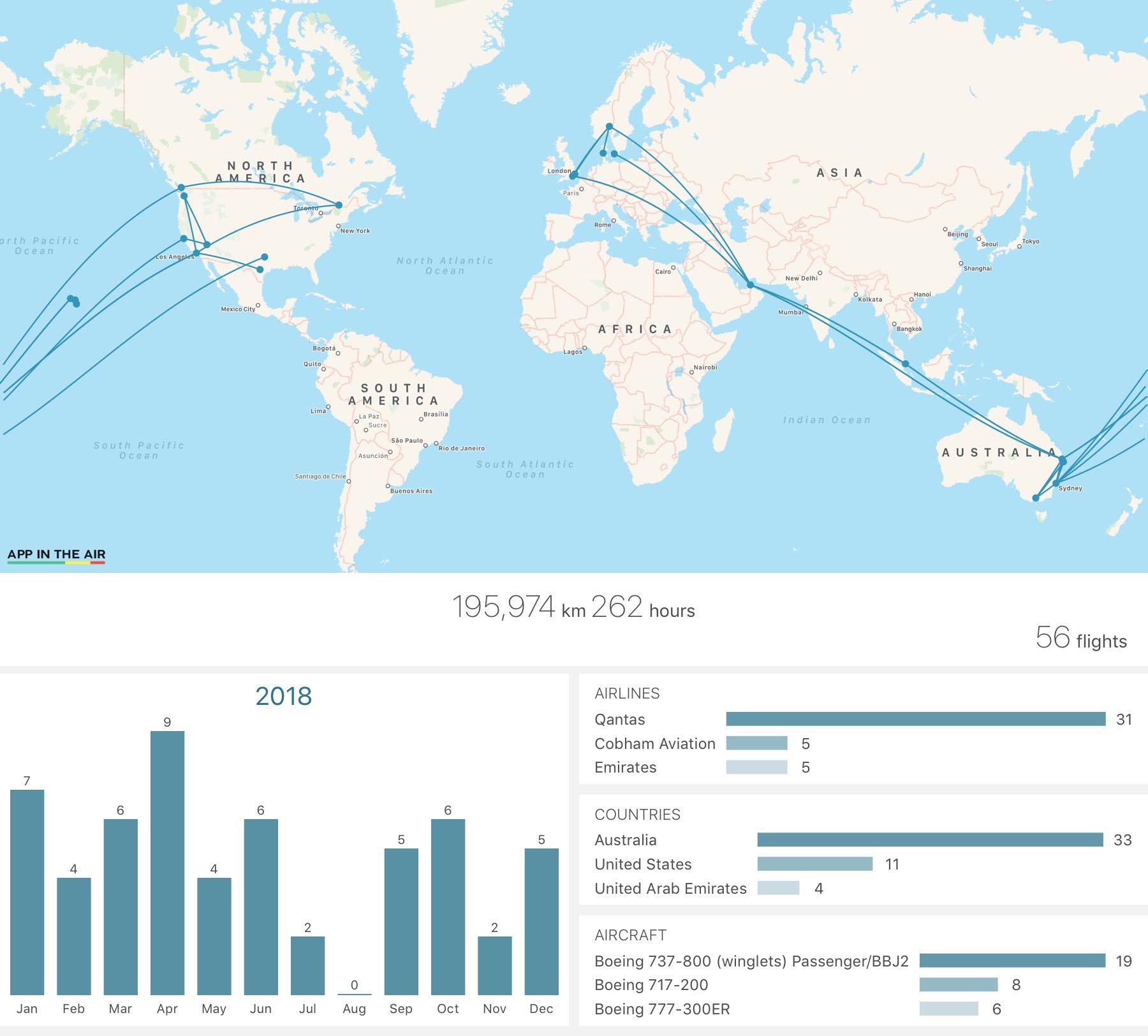
That's up 15,000km, 17 hours and 3 flights from last year. So yes, travel went up but I also did a bunch of remote workshops which helped keep that down, as well sending Scott Helme to run in-person ones that contributed to keeping me on Aussie soil.
Blogging
I actually got a bit of a surprise when I pulled the list of my most popular blog posts for 2018:
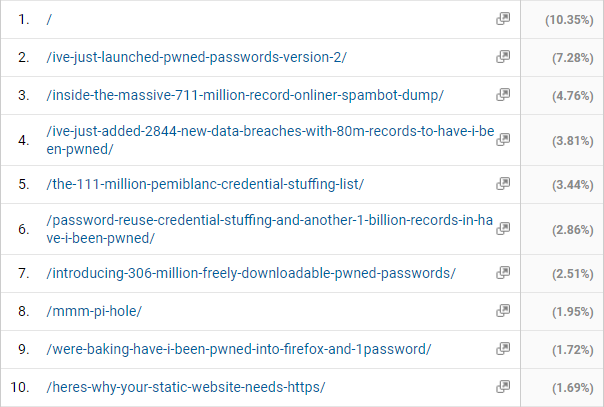
The surprise was that after the home page, the most popular page hit on my site was the one about Online Spambot, a post I published in August 2017. I guess it's maintained its traction due it being referenced in the HIBP description and there being a huge number of people finding themselves pwned. In fact, I'm sure that's why the next 3 blog posts are up there too because they're all from similar incidents (number 6 in that list was also from 2017).
If I'm honest though, my favourite post of the year was the one I published earlier this week on New Year's Eve - 10 Personal Finance Lessons for Technology Professionals. I love this post. I love the reaction it's had. I love that based on so much of the positive feedback I've had it might actually improve people's lives in away I don't think any previous post has before. Who knows, maybe this is something I'll even write more about in 2019 if there's an appetite.
The sponsorship model continued strongly too. It's been resoundingly well-received by both browsers to the site and the sponsors themselves and I've already booked 2019 out until August.
Speaking
Geez, where to start... Probably with my 2018 events page which lists everything I did of a public nature. What it doesn't do is list all the private events which pretty dramatically increases that list. Of the ones I can talk about, they included:
Microsoft in Copenhagen:
Thanks @troyhunt , fun and interesting talk in copenhagen today #happyaussieday #infosec #haveibeenpwned pic.twitter.com/vrNQNb6Po5
— Finn Strand (@finnstrand) January 26, 2018
MVP Summit in Seattle:
This is my first time hearing @troyhunt speak, he is giving a talk called {Hack Your Career}, and this is great info and extremely well delivered. #MVPBuzz #MVPSummit pic.twitter.com/P3hd15Sd5m
— Richard Hay (@WinObs) March 4, 2018
Ascend in Vegas:
Enjoying a keynote by @troyhunt at @episerver Ascend.#epidev #security #emvpbuzz pic.twitter.com/6MFRK3c0mC
— Henrik Fransas (@HenrikFransas) March 12, 2018
CRN Pipeline in Melbourne:
“This is like a mob shakedown.” CRN Pipeline 2018 speaker Troy Hunt discusses the extent to which breached data is compromised and resold to users on the web. #CRNpipeline @troyhunt pic.twitter.com/J3msdhCNEX
— CRN (@CRN_au) April 19, 2018
CRN Pipeline in Sydney:
@haveibeenpwned creator and security expert Troy Hunt tells #crnpipeline about how he was anonymously contacted by a data trader who had access to 1.3bn Australian Red Cross Blood Service records, including his own. The huge breach made headlines around Australia. @troyhunt pic.twitter.com/OfBPLDlShB
— CRN (@CRN_au) May 3, 2018
Loco Moco Sec in Hawaii:
@troyhunt had a great talk, he even used https://t.co/SKgRTcLW2e like a boss @LocoMocoSec pic.twitter.com/coOYwMY1ga
— Troy (@troyoholous) April 5, 2018
Infosecurity EU in London:
Day 2 @Infosecurity Europe, @troyhunt talks about how only 2% of businesses are using free technology to protect their websites by CSP #infosec18 pic.twitter.com/0ANNUl6ybD
— Will Painter (@WillPainter_) June 6, 2018
SSW in Sydney:
How safe is your #password?! I hope you tuned into #NETUG tonight to find out from security expert @troyhunt!! A huge thank you to Troy for presenting for us tonight. If you missed out, never fear, I’m sure SSW TV will post the video in the coming week! pic.twitter.com/jtHlTyJ9l6
— SSW / SSW TV (@SSW_TV) July 25, 2018
Cyber Edge in Sydney:
At #cyberedge and @troyhunt taking the stage. pic.twitter.com/bOv0fBXN44
— Chris Gatford (@ChrisGatford) July 26, 2018
SailPoint in Sydney:
@troyhunt hard at work at #spnav18 pic.twitter.com/iAMVdNO79x
— Lance Haeden (@LHaeden) August 22, 2018
API Days in Melbourne:
Troy Hunt @troyhunt speaking at his best, he shows that not all hackers come with hoodies and green command line screens, and how security is taken so lightly at even the bigger enterprises. #APIdaysAU pic.twitter.com/19lb65Xhkm
— Sagar Jani (@sagarajgmailco1) September 4, 2018
Fortinet in Sydney:
@troyhunt doing an excellent rockstar presentation on stage at #FortiExpress - as an ex-employee of both Fortinet and TalkTalk, deeply enjoyed this. pic.twitter.com/mK1j8H6Vuy
— Dave “Shockeh” Knowles (@_DaveKnowles) September 5, 2018
TECHpalooza on the Gold Coast:
We’ve got a password problem. @troyhunt is here to help. Using tools like 1Password and FaceID will help. #techplza @TECHpaloozaGC pic.twitter.com/e4HSzwyuxX
— Carl Hooker (@mrhooker) October 3, 2018
Texas Cyber Summit in San Antonio:
Watching @troyhunt talking about Have I been pwned at @texas_cyber pic.twitter.com/F5zRMhHst6
— Joe Parker (@joesparker) October 12, 2018
Dev Fest Weekend in Dallas:
Finally! @troyhunt’s talk on security! #DevFestWeekend2018 pic.twitter.com/FfhXKDnjJA
— Chris Benard (@cbenard) October 13, 2018
Sibos in Sydney:
#Sibos Big Issue Debate @troyhunt at Hacker: I have an objection to the thought that increasing security makes things harder. There are technologies that achieve both objectives. We need to help people understand that the technologies are there and use them effective. pic.twitter.com/XaYneE72fJ
— Sibos (@Sibos) October 23, 2018
There were a bunch of NDCs to do, starting with London in Jan:
Our Emy Spjuth is currently at the NDC London conference listening to some high quality talks and enjoying the new knowledge. She says that the talk from Troy Hunt is just one example of all the great things she is learning today. #knowledge #tretton37 #ndclondon @troyhunt pic.twitter.com/2OIX12ZbvR
— tretton37 (@tretton37) January 18, 2018
Then Oslo for NDC security:
Kicking #NDCSecurity off with @troyhunt @NDC_Conferences pic.twitter.com/ULzNtKjeqz
— Zoë Rose (@5683Monkey) January 24, 2018
My home on the Gold Coast in May:
Beautiful spot for @NDC_Conferences today ? https://t.co/F7IKiLkvBE pic.twitter.com/0sYt13CVtF
— Troy Hunt (@troyhunt) May 15, 2018
And then Oslo again in June (incidentally, seen here doing my new favourite talk "Everything is Cyber-Broken" with Scott):
Looking up to a hilariously funny closing session of #NDCOslo by @troyhunt and @Scott_Helme “Everything is Cyber-broken” @NDC_Conferences
— Adi Shavit (@AdiShavit) June 15, 2018
[a view from the pit] pic.twitter.com/M22nSuJV2y
And Sydney in September:
It's time for @troyhunt at @NDC_Conferences Sydney and up on stage with him is @letsencrypt! pic.twitter.com/JfqvsMkN17
— Scott Helme (@Scott_Helme) September 19, 2018
Spending time at the Australian Cyber Security Centre here in Aus was also a wonderful experience:
@haveibeenpwned’s @troyhunt speaking to ACSC staff about #databreaches. pic.twitter.com/FQfJOPb4OE
— Australian Cyber Security Centre (@CyberGovAU) August 10, 2018
And just to top it off, a keynote appearance in Microsoft Connect (albeit recorded from Aus):
Busy day in the office ? pic.twitter.com/qPWGwX8PE0
— Troy Hunt (@troyhunt) November 13, 2018
And, yeah, I think that's all it was! Actually, it could have been much busier, I declined 76 events:
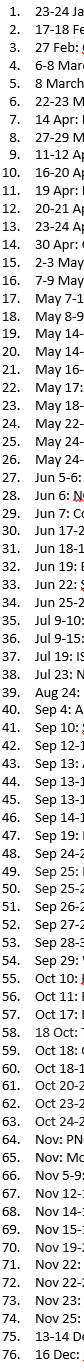
I do actually keep track of all these and as it turns out, that's just 1 more event than I declined in 2017. I'm surprised about how closely these 2 years have tracked to each other in so many ways.
Why No HTTPS?
2018 was a great year for HTTPS. Looking at Scott's 2018 Alexa Top 1M analysis from August (his most recent 6-monthly publication), 52% of the world's top 1M sites are now served over HTTPS by default. On the one hand, we're only just past the half way point but on the other hand, it was only 31% a year earlier.
Because public shaming of poor security drives positive changes (a popular 2018 blog post that will get a lot of mileage for years to come), we made Why No HTTPS to call out the largest offenders both globally and per country:

The positive stories are the ones you don't see here; the ones that are no longer on the list. Site like the ABC in Australia, the Daily Mail in the UK and Roblox in the US. They're the largest sites in their respective countries to drop off the list and there have been many, many more in the same boat. I've actually had developers from many organisations reach out requesting that the list be refreshed just so their site drops off. Shaming works in powerful ways ?
HTTPS is Easy
I didn't want to just shame organisations doing the wrong thing, I also wanted to help everyone get better at HTTPS. After all, HTTPS is easy, so I built HTTPS Is Easy:
This became a great 4-part reference series with 5-minute videos which live up to the title. I'm enormously happy with how it was received, and frankly a bit overwhelmed that the community stepped up and translated it into 19 different languages including: Czech, Danish, Dutch, English, Estonian, Finnish, French, German, Greek, Indonesian, Italian, Norwegian, Persian, Polish, Portuguese, Russian, Slovenian, Spanish and Swedish. That's pretty awesome!
Have I Been Pwned
Geez, were to start on this one... In point form:
- Added 76 new data breaches
- Which encompassed 829,391,906 additional records
- Signed up 445,720 new subscribers
- Sent 1,224,377 breach notification emails to them
- And sent another 239,277 notifications to those monitoring domains
- Got the UK government on-boarded to monitor all gov domains
- Got the Aus government on too
- And the Spanish government
- Had the Estonian Police Force use it to notify their citizens
- Partnered with 1Password
- Integrated into both Firefox and 1Password
- Made stickers!
And probably 100 other things that should be in a retrospective but just flew by in a blur! But there was another aspect of HIBP which really took off in 2018 and it deserves its own heading:
Pwned Passwords
When I launched version 2 in Feb, this service really started to get traction. The k-anonymity model courtesy of Cloudflare was the real killer feature and a special mention goes to Junade Ali on that:
Great catching up @troyhunt at the @Cloudflare today - in front of the famous lava lamp wall. pic.twitter.com/4KDQfhUfWy
— Junade Ali (@IcyApril) March 15, 2018
If you don't know the back-story on those lava lamps, this is a fun vid that's only a few minutes long:
Back to Pwned Passwords, the premise of checking to see if a password has been previously breached before allowing someone to use it has gained a lot of traction. I've seen dozens of use cases first hand (and there's probably hundreds I'll never know about), with EVE Online being the first big one:
Here is the message we display to our users during login if we find their password in the @haveibeenpwned list. We try to explain calmly what is wrong and how to fix it. Provide links and guidance. pic.twitter.com/9rc8svI0yS
— Stefán Jökull Sigurðarson - CCP Ghostrider (@stebets) July 12, 2018
Okta built an absolutely awesome browser extension:
Why I like @Okta's Passprotect plugin: if sites use outdated password complexity rules and tell people that "P@ssword1" is a good password, the plugin still warns the password is unsafe. It uses @troyhunt's pwned passwords and the k-anonimity model to securely check the password pic.twitter.com/wBFWMzrtra
— John Opdenakker (@j_opdenakker) August 27, 2018
And GitHub downloaded the hashes (freely available to everyone) and rolled it into a platform most of you reading this will be very familiar with:
You could also use the Have I Been Pwned API (https://t.co/dkDGNKtKdY) to require users with _compromised_ passwords to change those, like GitHub does (https://t.co/Nr7Bf2Oox8). pic.twitter.com/4qbt8mvWVs
— Paul Schreiber (@paulschreiber) September 4, 2018
Of those who do consume the k-anonymity API, I'm usually serving up somewhere between 4 and 6 million requests a day:
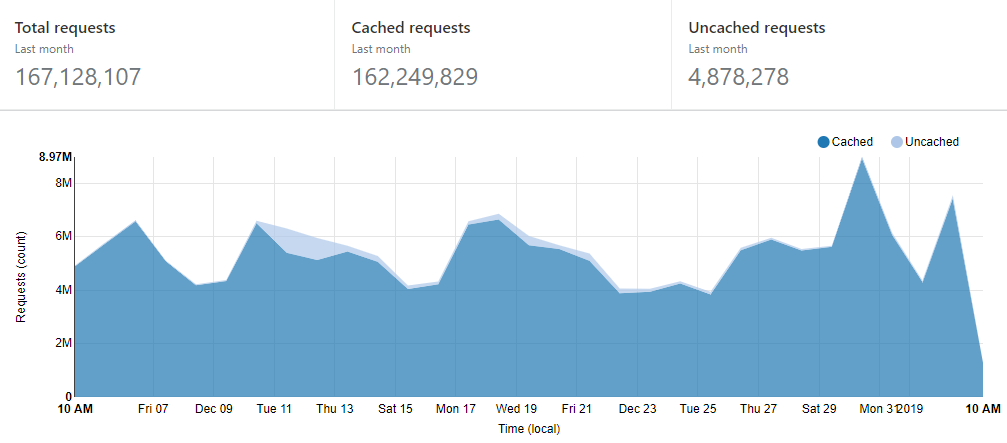
There were a couple of cache flushes in there but just to give you a sense of how well optimised the service is to serve content directly from Cloudflare's edge nodes and not hit the origin server, here's the last week:
That's a 99% cache hit ratio ?
Report URI
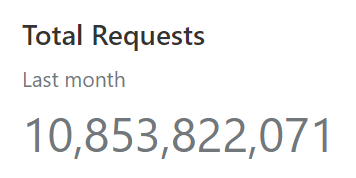
Scott wrote a year in review piece this week so I'll defer to his overview for that but in short: heaps of new reporting types, a wizard that makes creating CSPs way easier, the launch of Report URI JS, heaps of both free subscriber and commercial customer growth and we're also pushing a few reports through these days too:
But the highlight - without a doubt in my mind - is covered in this next section:
Awards
What. A. Year! In fact, what a couple of weeks and it all began with AusCERT's Award for Information Security Excellence, presented in my home town:
.#AusCERT2018 Award for Information Security Excellence goes to @troyhunt @AusCERT 2018 Gala Dinner pic.twitter.com/9lxmwX0tdR
— Valdemar Jakobsen (@jamver) May 31, 2018
Then a week later I was in London and scoring the Grand Prix Prize for the Best Overall Security Blog alongside Scott Helme who also picked up a gong:
With @Scott_Helme (at a different awards night) learning we both just scored at the European Cyber Security Blogger Awards! pic.twitter.com/RbCoLsKTja
— Troy Hunt (@troyhunt) June 5, 2018
And then, a mere few more hours on at a different event:
We won! @reporturi won! #scawards2018 pic.twitter.com/E65XjpQJvQ
— Troy Hunt (@troyhunt) June 5, 2018
It was, by any reasonable measure, a surreal experience. I can't imagine topping that again.
But as well as those ones there was my 8th Microsoft MVP award and my Regional Director status was also renewed. These have both been marvellous programs to be a part of over the years and I'm proud to have that ongoing association with Microsoft.
What's Next
I'm 2 weeks to the day out from heading back to Europe so the whole show starts again very soon. In many ways, 2019 will be more of the same but in other ways, there's a bunch of new things on the horizon. I've already committed to events in 3 new places I've never been before in the first half of the year so that'll be cool.
Beyond that, I honestly don't know. I have a view about 6 months out around travel commitments but the nature of this industry and indeed the role I play today is that I have absolutely no idea what will pop up overnight, let alone further along into 2019. But that's ok, it keeps things entertaining ?